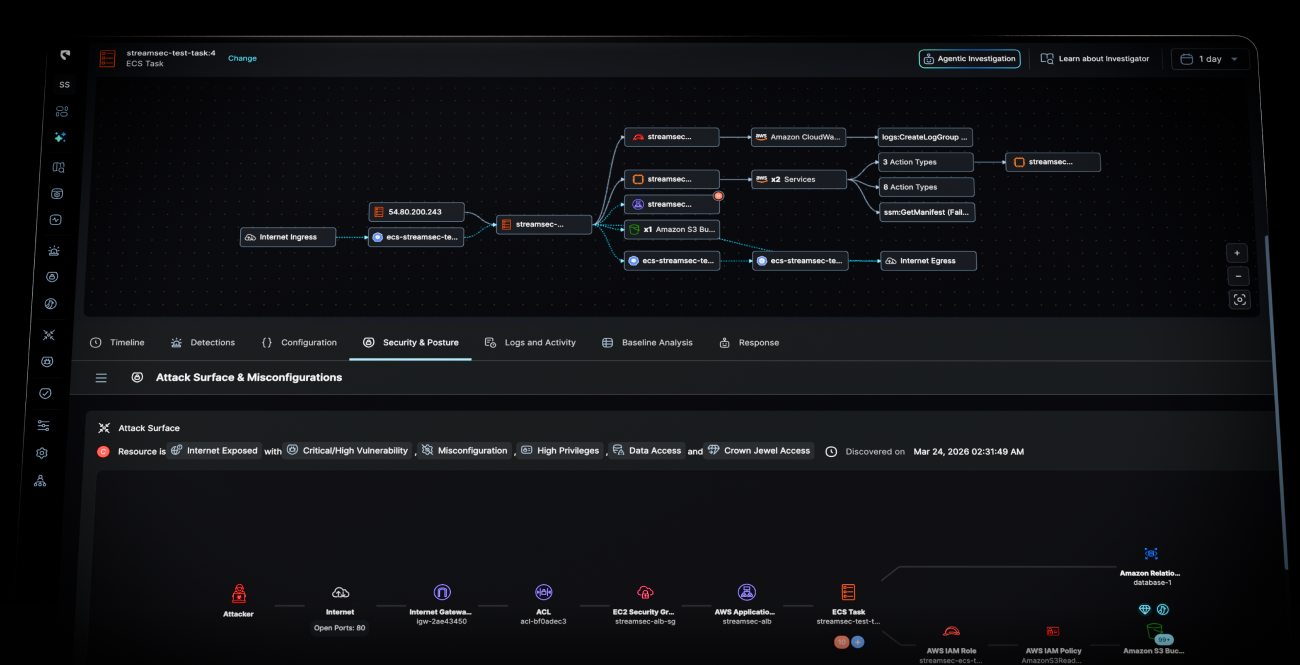
Every asset and its live state
Always know exactly what exists in your cloud, what it’s doing, when it changed, and the risk it introduces — all in real time.

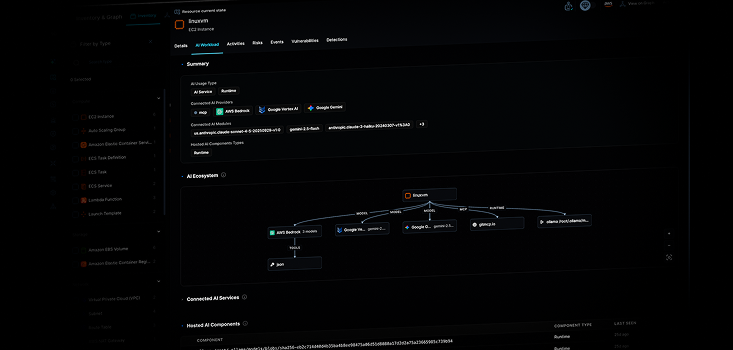
AI Workload Discovery
Deep visibility and insights across your entire AI and agent landscape. From models to mcp and tools.
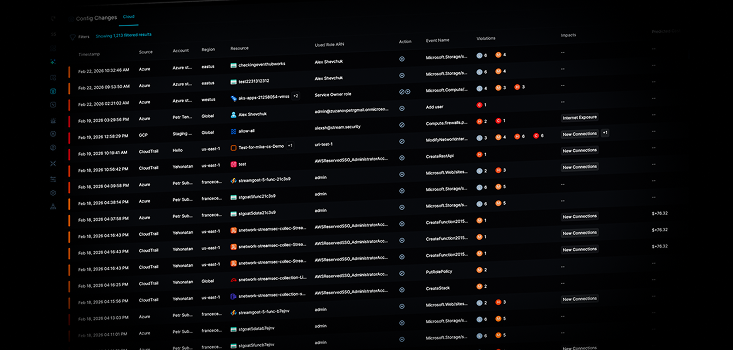
Most tools show you what changed. Stream shows you what it means.
Every configuration change is automatically mapped to its security impact - internet exposure, privilege escalation, attack path creation, the moment it's ingested.
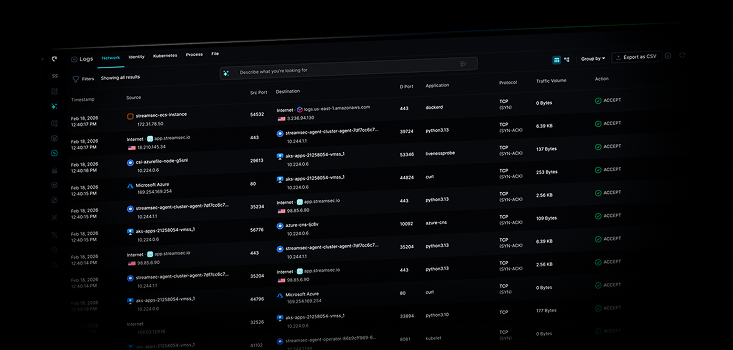
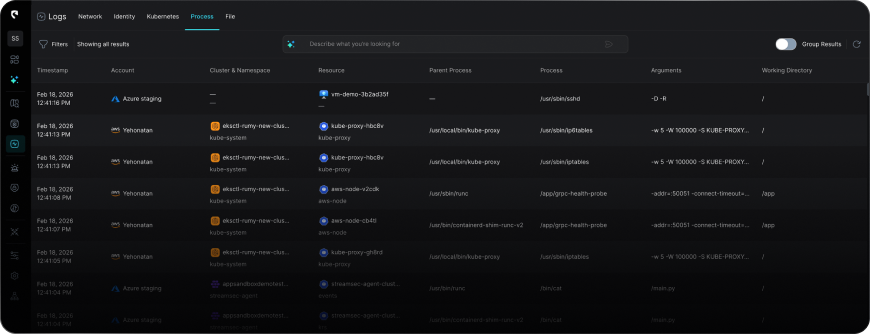
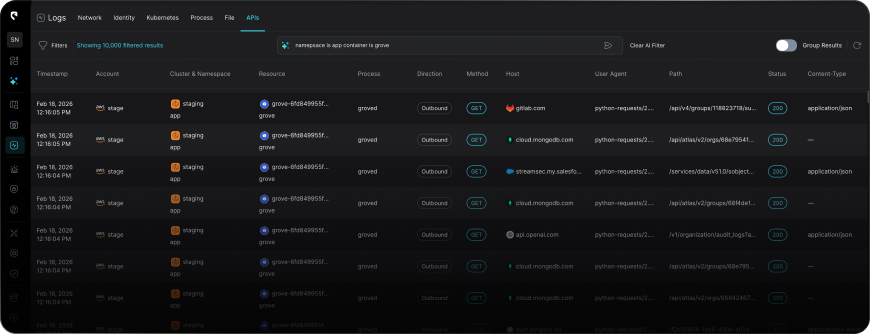
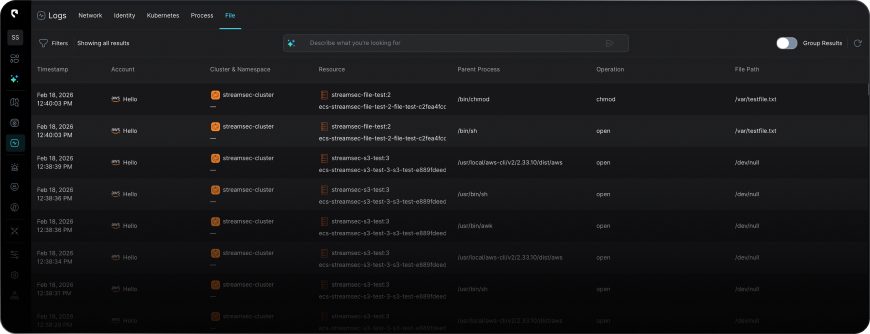
Full audit activity, enriched before you ever see it.
Every action resolved to the actual executing identity or workload, with complete log enrichment not a raw event string.


.png)


