
From Shadow AI to Detection and Response: Closing the Visibility Gap at Machine Speed
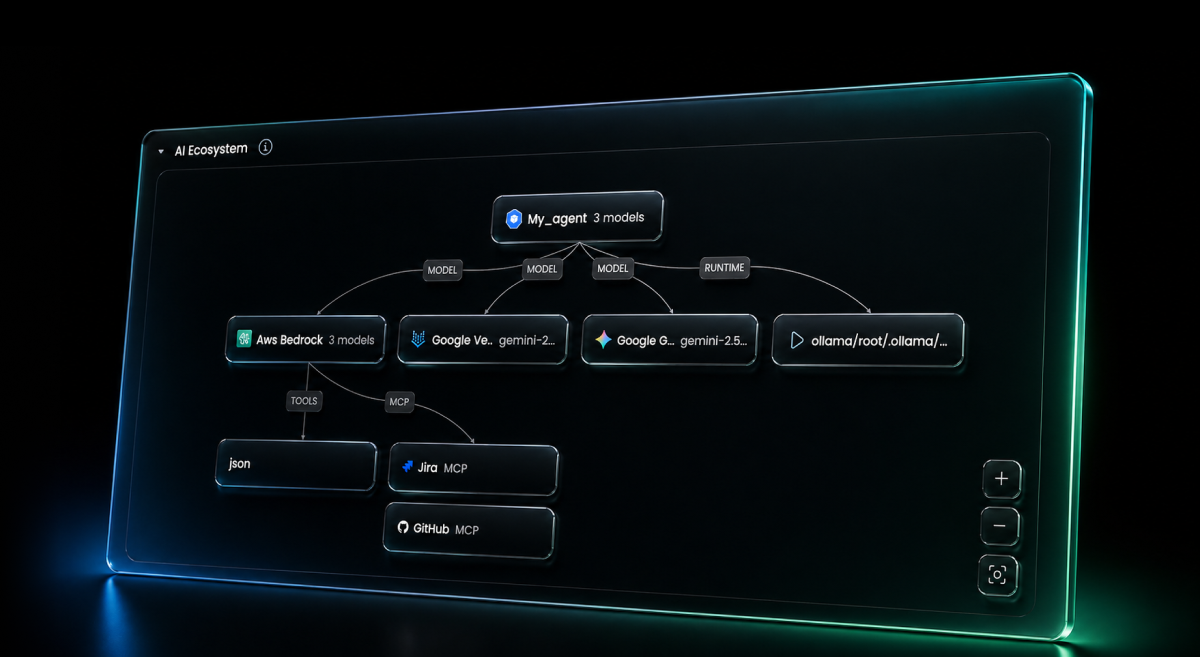
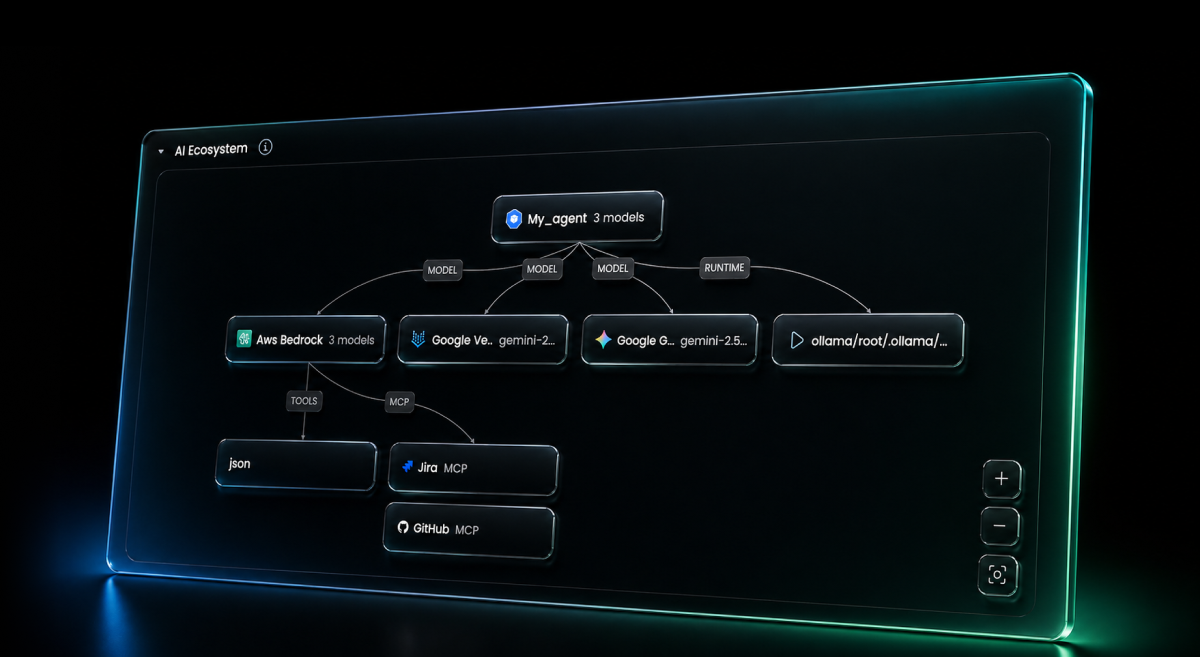
AI workloads are running across your cloud right now, models, agents, tools, MCP servers —most of them invisible to security. Stream's AI workload discovery doesn't just inventory them. It detects how they behave, computes the blast radius the moment something goes wrong, and triggers response across the AI layer. From a new MCP server appearing in production to a privileged identity invoking an LLM for the first time, you see it, you understand the impact, and you contain it — in under five minutes.
It's 2:47 AM. A backend service in your production VPC starts making outbound calls to a Bedrock endpoint it has never touched before. Thirty seconds later, that same workload's IAM role — a role with read access to your customer database — invokes a foundation model with a tool-use schema attached. The tool calls an internal API. The API returns customer records. The records flow into the model's context. The model responds.
Your CSPM saw a Lambda execute. Your CWPP saw a process run. Your SIEM saw a few API calls. None of them saw the attack.
This is shadow AI, and it operates at machine speed.
AI adoption didn't happen gradually. It exploded.
Foundation models. Hosted APIs. Agents. Copilots. MCP servers. They're now embedded in every application — backend services calling LLMs, agents making decisions and taking actions, developers wiring tools and integrations into pipelines.
And they don't behave like traditional infrastructure:
Traditional tools weren't built for this. They show you a container running, an API call executed, a role assumed. They don't tell you which model was invoked, which tools were connected, which MCP servers are wired in, which data is flowing through, or whether any of it is normal.
So AI spreads silently — until something goes wrong.
Discovery is the foundation. But discovery alone is an inventory — and inventories don't catch attackers.
Stream's AI workload discovery captures every AI component in your environment using cloud-native logs (network, DNS, audit, SaaS) and runtime telemetry at the API payload layer. Then it does the harder work: it correlates each component to the workload executing it, the identity behind it, and a behavioral baseline of how it normally operates.
That correlation is what makes detection possible. The signals we surface include:
New model invocations from previously non-AI workloads. A Lambda function that has never called Bedrock suddenly invokes a foundation model. That's a baseline change worth a closer look — especially when the workload's identity has access to sensitive data.
Unapproved MCP server connections. New JSON-RPC traffic from a workload that wasn't baselined as agentic. Most environments have a small, known set of MCP servers. New ones appearing in production are almost always either shadow deployments or compromised infrastructure.
Privileged identities invoking AI services. When an admin role, a CI/CD identity, or a workload with broad data access starts invoking foundation models, the blast radius of any prompt injection or tool abuse just expanded dramatically. Stream surfaces this the moment it happens.
Prompt injection and jailbreak signatures in API payloads. Detection rules running against Bedrock and Azure OpenAI HTTP traffic flag injection patterns, jailbreak attempts, data exfiltration prompts, and agent hijacking signals — at the payload layer, before the model has a chance to respond.
Anomalous agent behavior. Agents have characteristic tool-call patterns. When an agent suddenly chains dozens of tool calls instead of its baseline handful, or starts invoking tools it has never touched, that's not normal autonomy — that's an indicator.
Every detection is grounded in the workload, the identity, and the baseline. No standalone AI signals floating in a separate console. No "AI security" silo to triage on top of your cloud detection backlog.

Detection without response is just better-formatted alert fatigue.
The moment Stream detects something risky on the AI layer, CloudTwin® — Stream's real-time deterministic model of your entire environment — computes the blast radius immediately. Not by querying APIs. Not by waiting for the next scan. The model is already there.
That means we can answer, in real time:
Then response: revoke the identity, isolate the workload, block the model endpoint, kill the network path, or quarantine the MCP server — surgically, with full understanding of downstream impact.
From the moment a new MCP appears in production to the moment it's contained: under five minutes.
That's the difference between visibility and response.
Here's what an AI-layer attack looks like when you can see across the whole stack:
A developer commits code that pulls a new MCP server image from a typo-squatted registry. CI/CD deploys it into staging, where it inherits the staging workload's IAM role — a role that, due to a permissions drift two sprints ago, can read from a production S3 bucket.
Stream sees the new MCP server appear. New JSON-RPC traffic from a workload not previously baselined as agentic. The MCP exposes tools to a downstream agent running in the same cluster. The agent receives a benign-looking prompt from a user-facing chatbot — but the prompt contains an indirect injection chained from a document the user uploaded.
The injected prompt instructs the agent to use its new MCP tool. The tool uses the workload's IAM role to read from S3. Customer records flow back through the agent's context.
In a traditional stack, this is six disconnected events across six different tools — discovered weeks later in a forensic review.
In Stream, it's one storyline. The new MCP, the inherited identity, the prompt injection signature in the API payload, the unusual S3 read, the data exfiltration path — all correlated, all visible, all contained before the records leave the environment.
This is what AI Detection and Response actually means.
Stream's AI-layer detections map directly to MITRE ATLAS — the adversarial threat framework for AI systems:
This isn't a separate AI security product bolted onto your cloud detection. It's your cloud detection platform, extended with the signals, context, and response actions the AI era demands.
AI is becoming part of every workload. Every backend service is one prompt away from being an LLM client. Every developer is one library import away from running an agent. Every workload is one IAM permission away from being a high-blast-radius AI target.
The attack surface is already here:
Without visibility, you're blind. With only visibility, you're documented but defenseless. With detection and response that understands the AI layer as a first-class part of your cloud — you have control.
Stream Security is an AI Detection & Response (AI DR) company built for the era of AI-driven environments across cloud, on-prem, and SaaS. As AI agents operate with real permissions and attackers move at machine speed, Stream enables security teams to keep pace by continuously computing a real-time, deterministic model of their entire environment. Powered by its CloudTwin® technology, Stream instantly understands the full impact of every action across identities, permissions, networks, and resources, allowing organizations to detect, prioritize, and safely respond to threats before they propagate. This transforms security from reactive detection into a true control plane for modern infrastructure.


