.png)
Stream Security Expands Beyond Cloud-Native: Full Hybrid Cloud Visibility with VMware, NSX, and On-Prem Network Support


Stream Security now extends CloudTwin beyond public cloud to VMware, NSX, and on-prem network devices. You get full attack path analysis, runtime threat detection, and real-time topology modeling across your entire hybrid environment - not just the cloud or on-prem part of it.
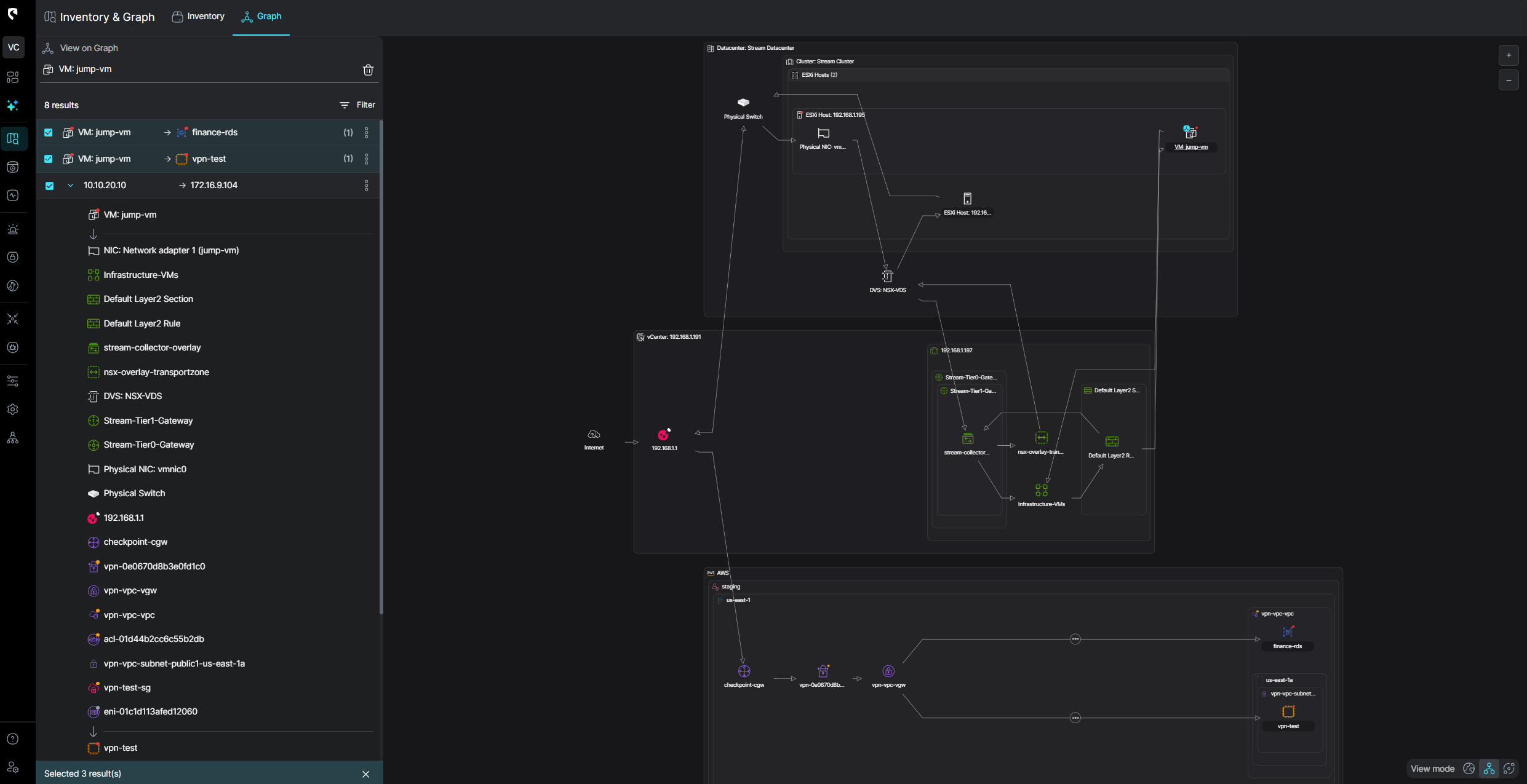
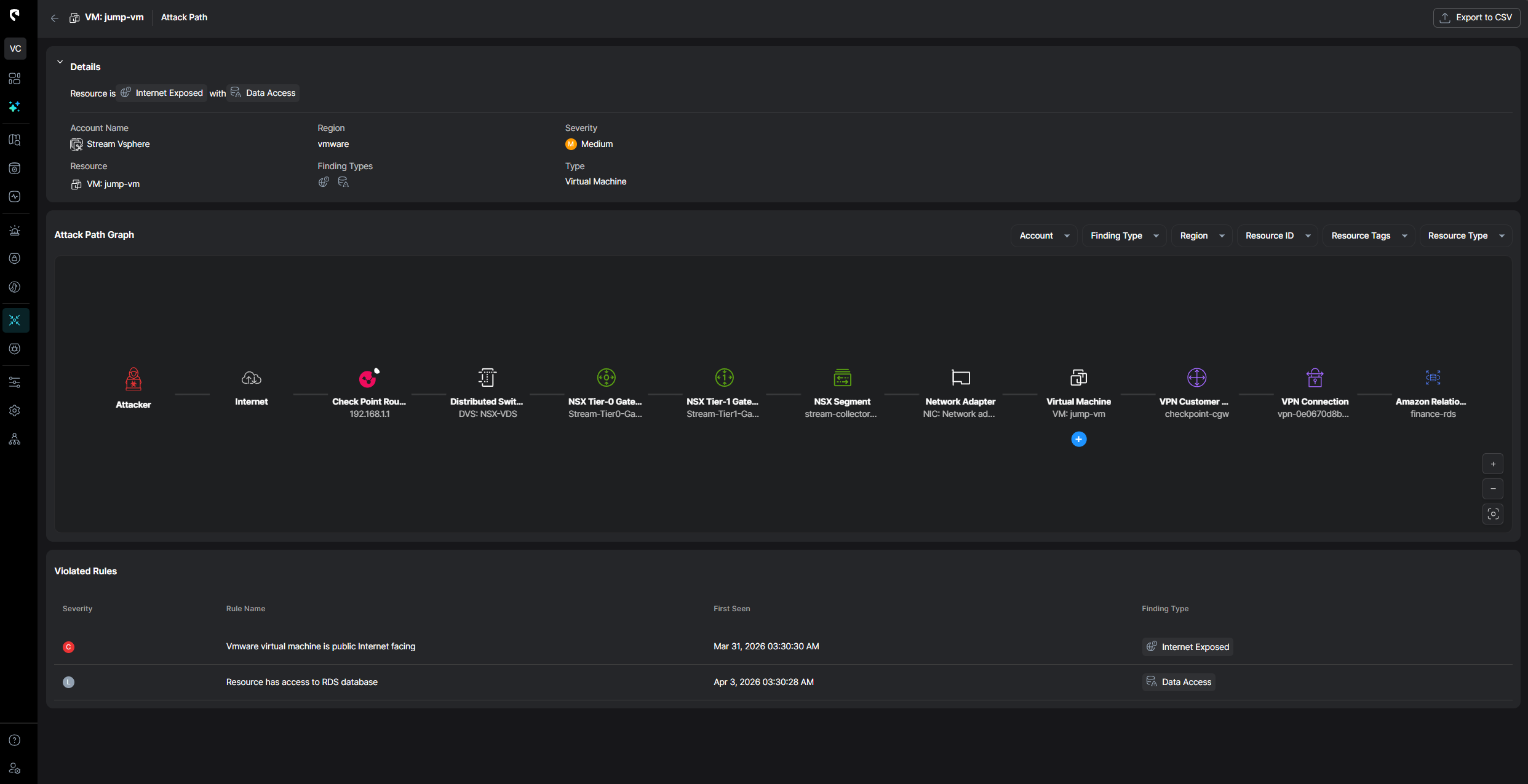
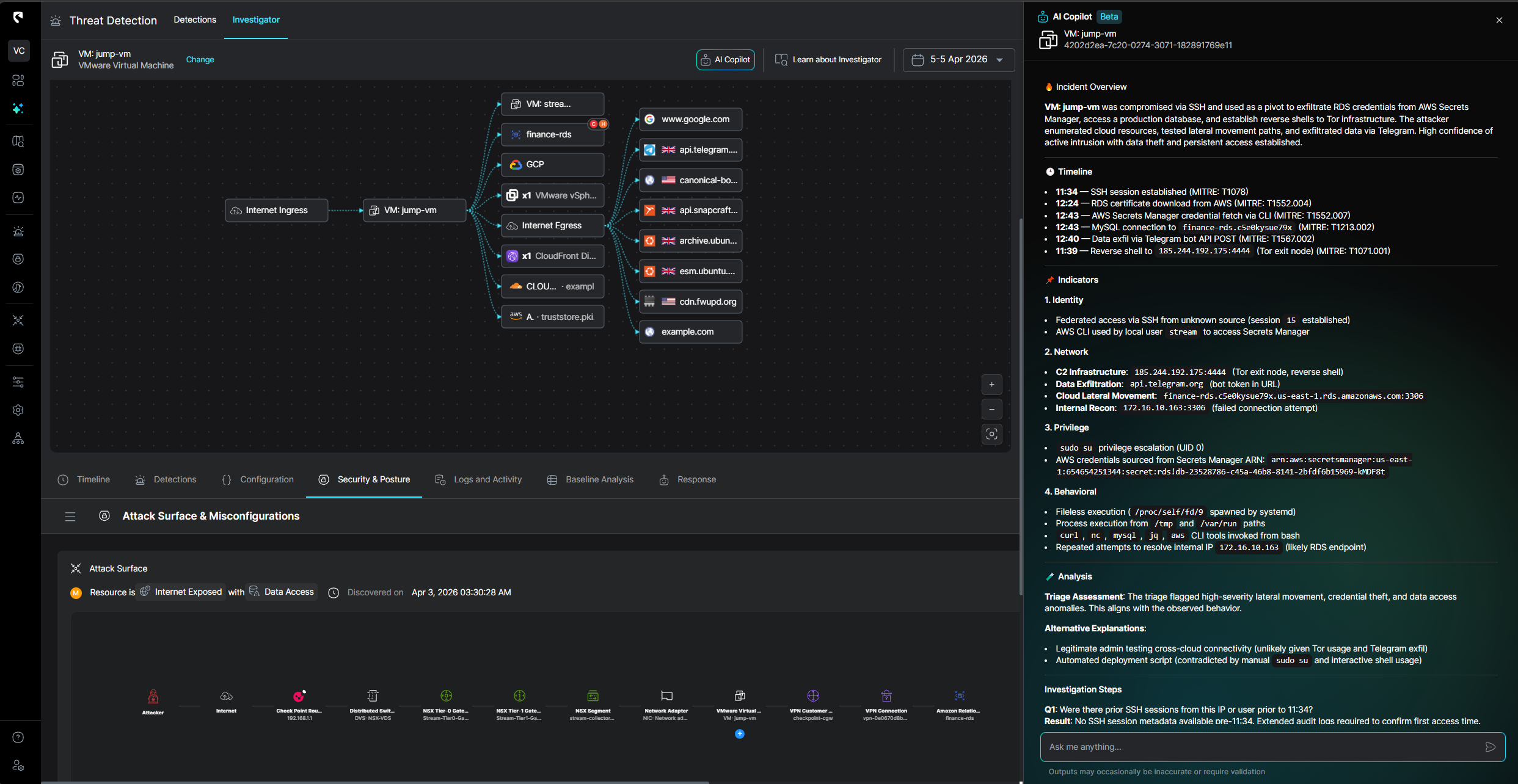
CloudTwin, Stream's real-time digital twin of your infrastructure, now models VMware environments, NSX network policies, and on-prem networking devices alongside your cloud resources. This means Stream can trace complete attack paths that cross environment boundaries such as a compromised VM instance that can reach an RDS in AWS through a misconfigured network segmentation

Stream ingests and correlates native VMware audit logs, vCenter events, and ESXi system logs in real time. Combined with NSX network flow data, we detect threats that VMware-only and cloud-only tools miss:
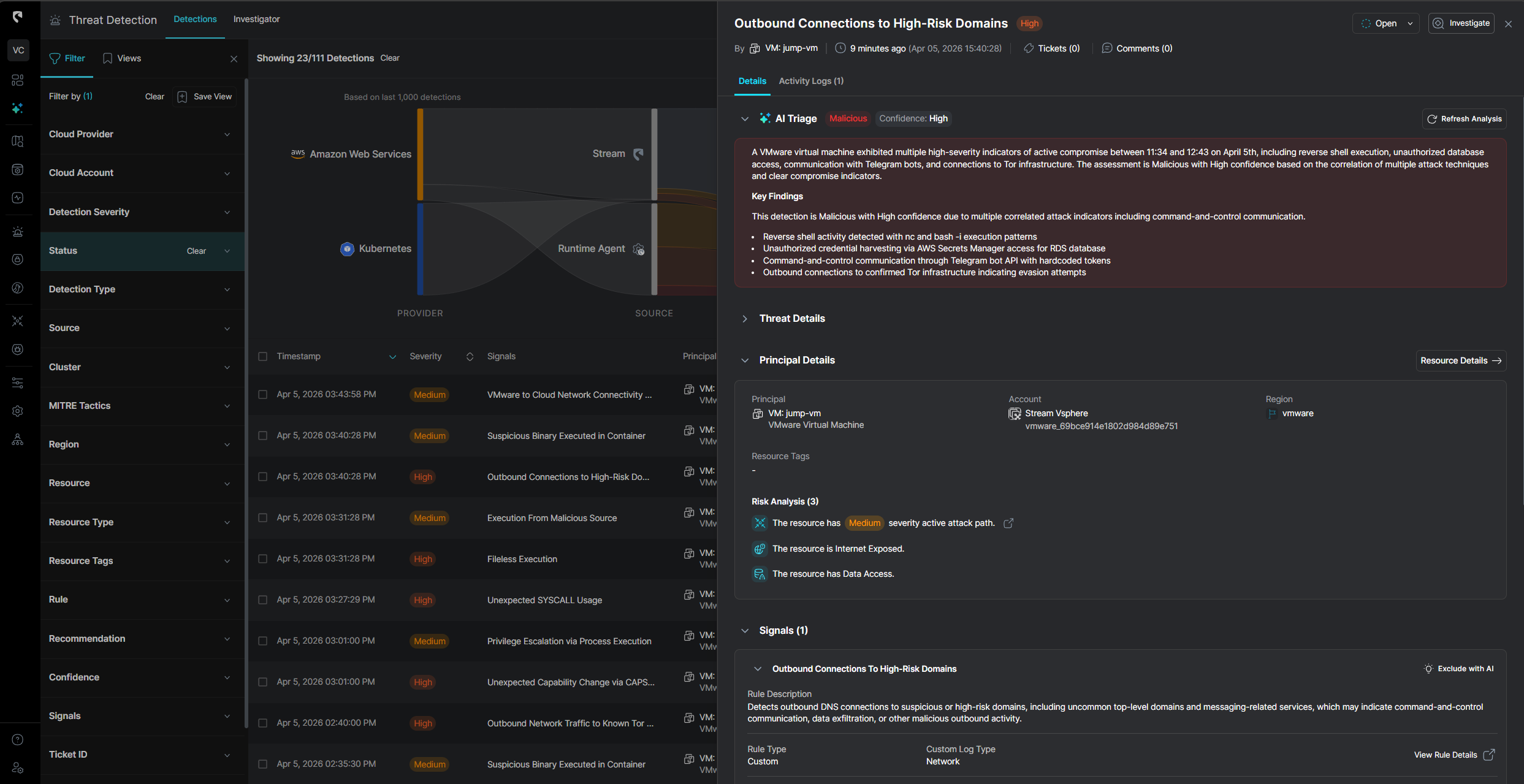
For workloads that need deeper inspection, Stream's eBPF-based runtime sensor extends into hybrid environments, delivering:
This gives security teams the ability to detect threats at every layer — from network routing to API payloads to process execution — regardless of where the workload runs.
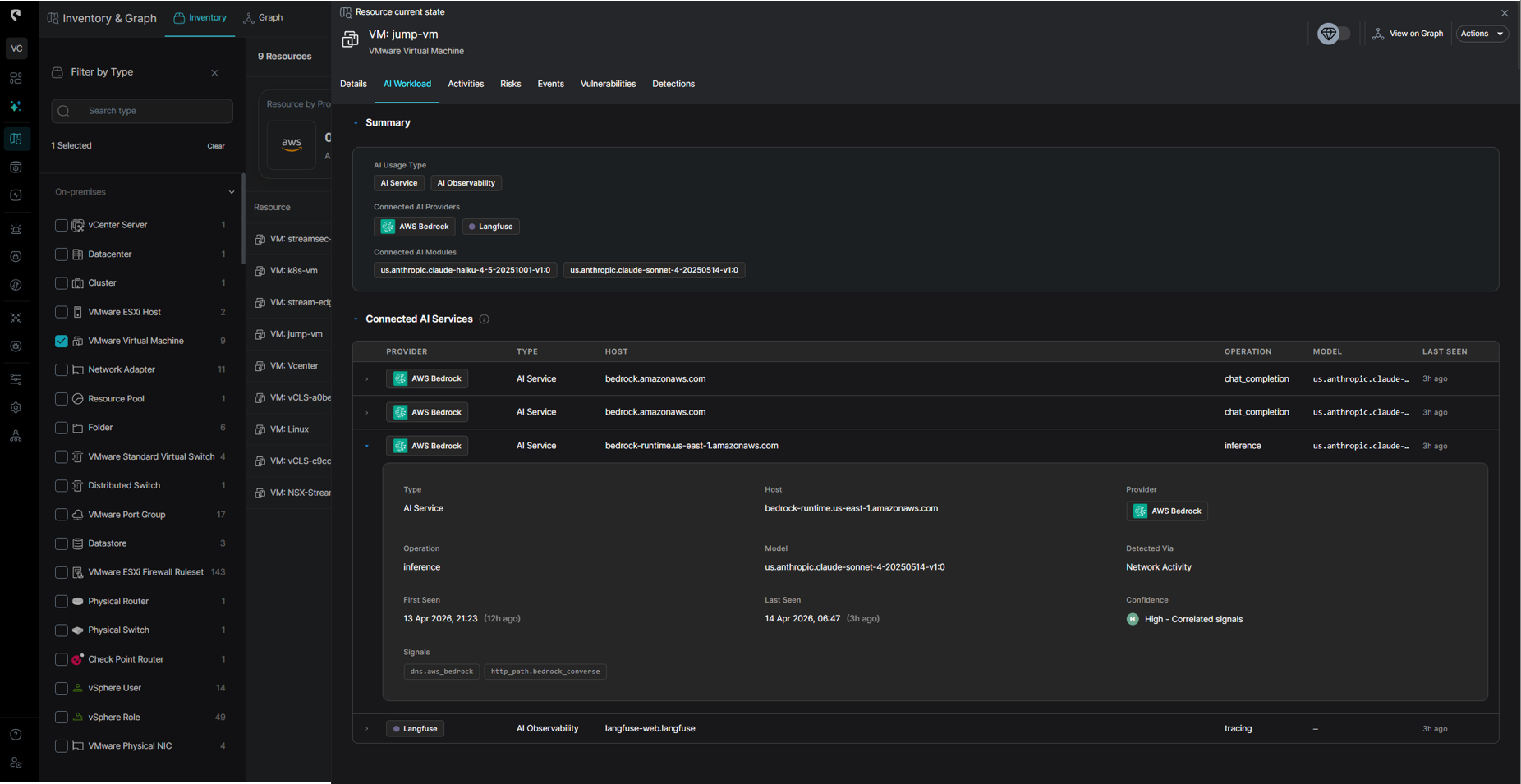
Detect and secure AI agents and workloads across your entire infrastructure, including both third-party services and self-hosted components.
Routers, switches, and firewall appliances are now first-class citizens in CloudTwin. Stream ingests device configurations, routing tables, and ACLs to:
Adding VMware and on-prem support isn't about checkbox compliance. It's about building the only security model that reflects how hybrid infrastructure actually works, and how attackers actually exploit it.
CloudTwin continuously maintains a living model of your entire environment: cloud resources, IAM relationships, network topology, VMware clusters, NSX policies, and on-prem routing. When something changes — a new firewall rule, a modified router ACL, a shifted NSX policy — Stream updates the model in real time and re-evaluates every attack path.
This is what allows Stream to go from alert to response in under 5 minutes — even when the attack spans three environments and six network boundaries.
VMware and on-prem networking are the beginning. We're building toward a unified security model that covers every environment where enterprise workloads run, because attackers don't respect infrastructure boundaries, and your detection shouldn't either.
If your security team is struggling with visibility gaps between cloud and on-prem environments, we'd love to show you how we can help - Book a demo
Stream Security is an AI Detection & Response (AI DR) company built for the era of AI-driven environments across cloud, on-prem, and SaaS. As AI agents operate with real permissions and attackers move at machine speed, Stream enables security teams to keep pace by continuously computing a real-time, deterministic model of their entire environment. Powered by its CloudTwin® technology, Stream instantly understands the full impact of every action across identities, permissions, networks, and resources, allowing organizations to detect, prioritize, and safely respond to threats before they propagate. This transforms security from reactive detection into a true control plane for modern infrastructure.


.png)

.png)
