.png)
Stream Security Now Supports MongoDB Atlas Log Ingestion for Comprehensive Cloud Threat Detection
.png)
.png)
Extending real-time threat detection to your MongoDB Atlas environments
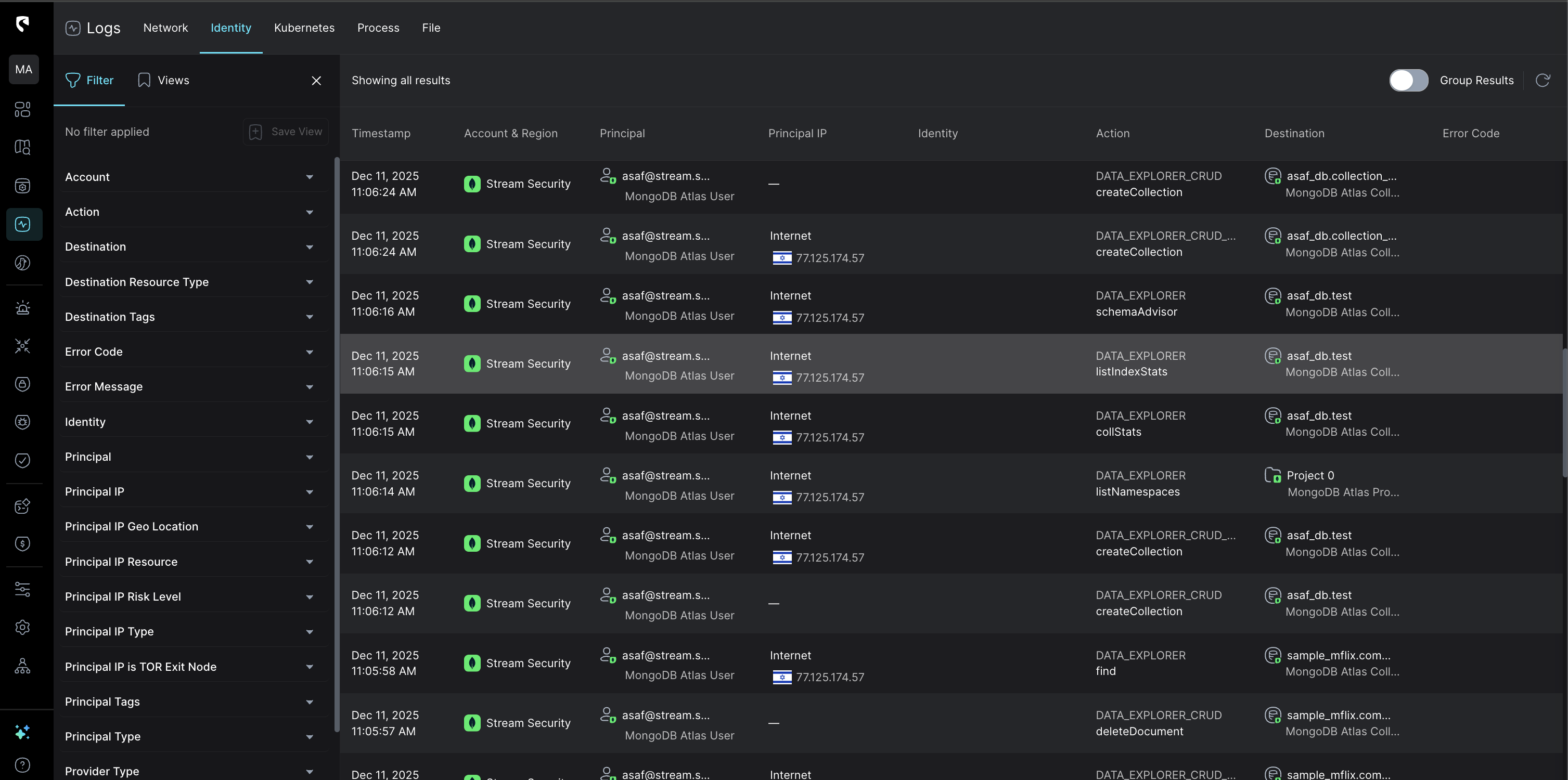
We're excited to announce that Stream Security now supports native log ingestion from MongoDB Atlas audit logs, bringing our real-time threat detection and response capabilities to one of the most widely adopted cloud database platforms.
MongoDB Atlas has become the database of choice for modern cloud-native applications, powering everything from startups to Fortune 500 enterprises. With this growth comes an expanded attack surface, and a critical need for security visibility into database activity.
Database-layer attacks remain one of the most damaging vectors for data breaches. Threat actors target MongoDB environments for credential theft, data exfiltration, privilege escalation, and unauthorized access. Without proper monitoring, these attacks can go undetected for weeks or months at a time.
With Stream Security's MongoDB Atlas integration, security teams can now:
The MongoDB Atlas integration enables detection of critical threats including:
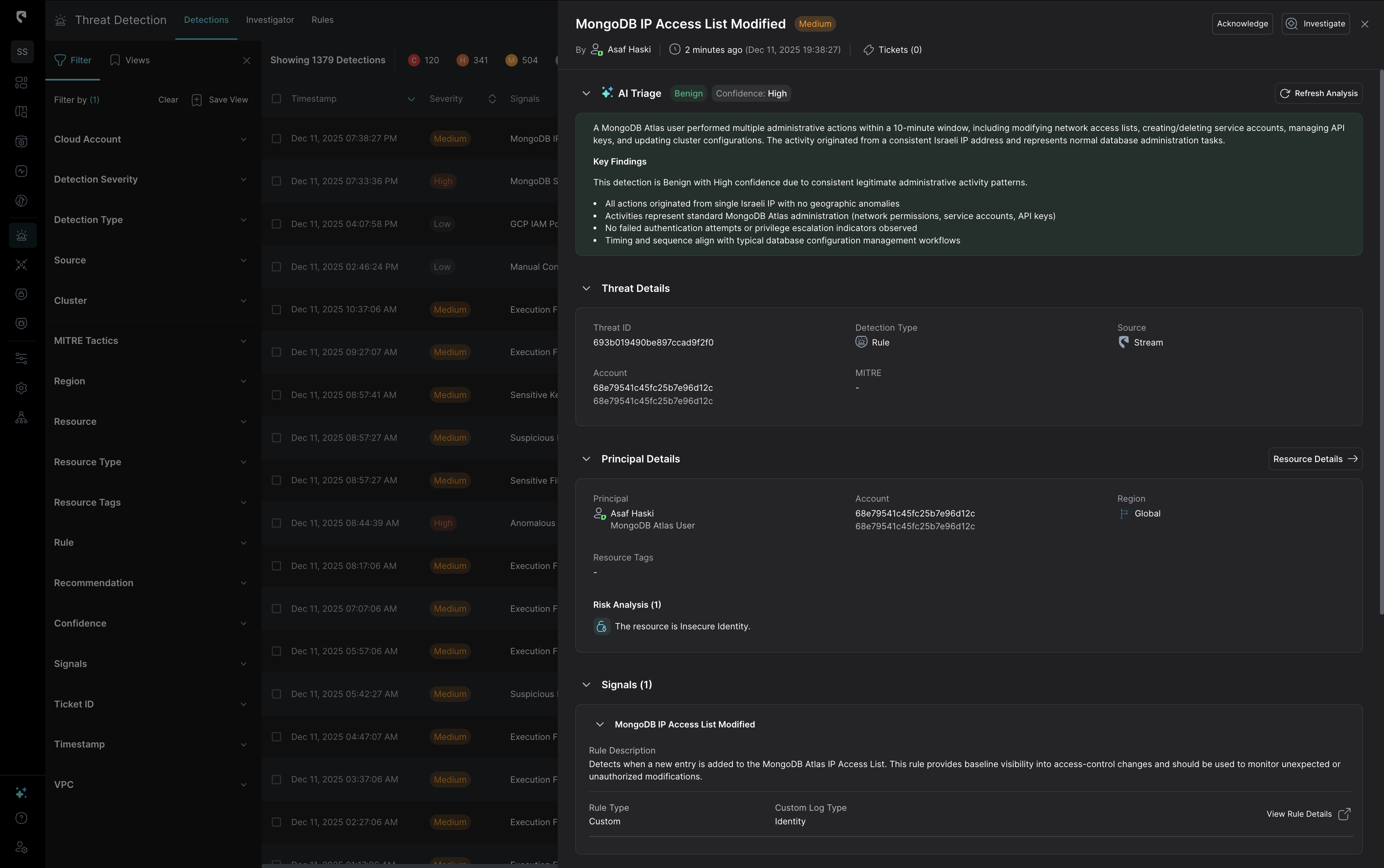
Getting started is straightforward. Stream.Security ingests MongoDB Atlas audit logs through native cloud integrations, requiring no agents or infrastructure changes. Once connected, you'll have immediate visibility into database activity with out-of-the-box detection rules tuned for MongoDB-specific threats.
The integration works alongside your existing Stream.Security deployment, enriching your cloud security posture with database-layer intelligence and enabling unified investigation across your entire cloud estate.
This release reflects our commitment to providing complete visibility across modern cloud environments. Your applications don't exist in silos, and neither should your security monitoring.
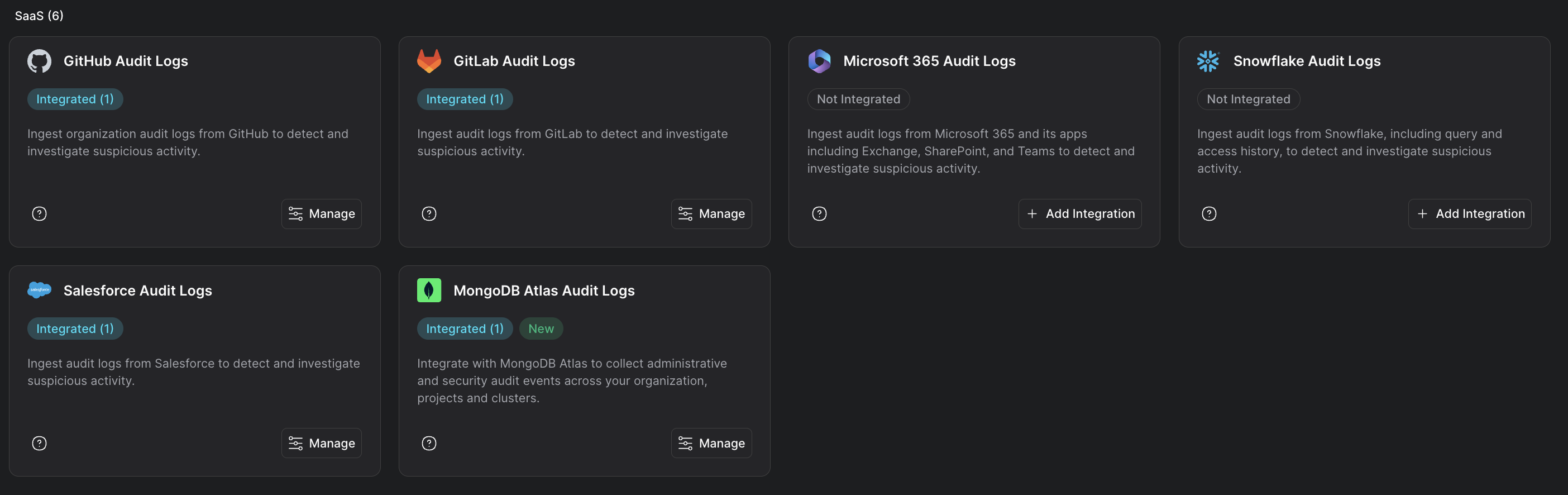
MongoDB Atlas joins our growing ecosystem of supported data sources, ensuring that wherever your data lives, Stream.Security has you covered.
Stream Security is an AI Detection & Response (AI DR) company built for the era of AI-driven environments across cloud, on-prem, and SaaS. As AI agents operate with real permissions and attackers move at machine speed, Stream enables security teams to keep pace by continuously computing a real-time, deterministic model of their entire environment. Powered by its CloudTwin® technology, Stream instantly understands the full impact of every action across identities, permissions, networks, and resources, allowing organizations to detect, prioritize, and safely respond to threats before they propagate. This transforms security from reactive detection into a true control plane for modern infrastructure.


.png)
