
Stream Security Now Supports OpenAI Platform Audit Log Ingestion for Comprehensive AI Control-Plane Threat Detection
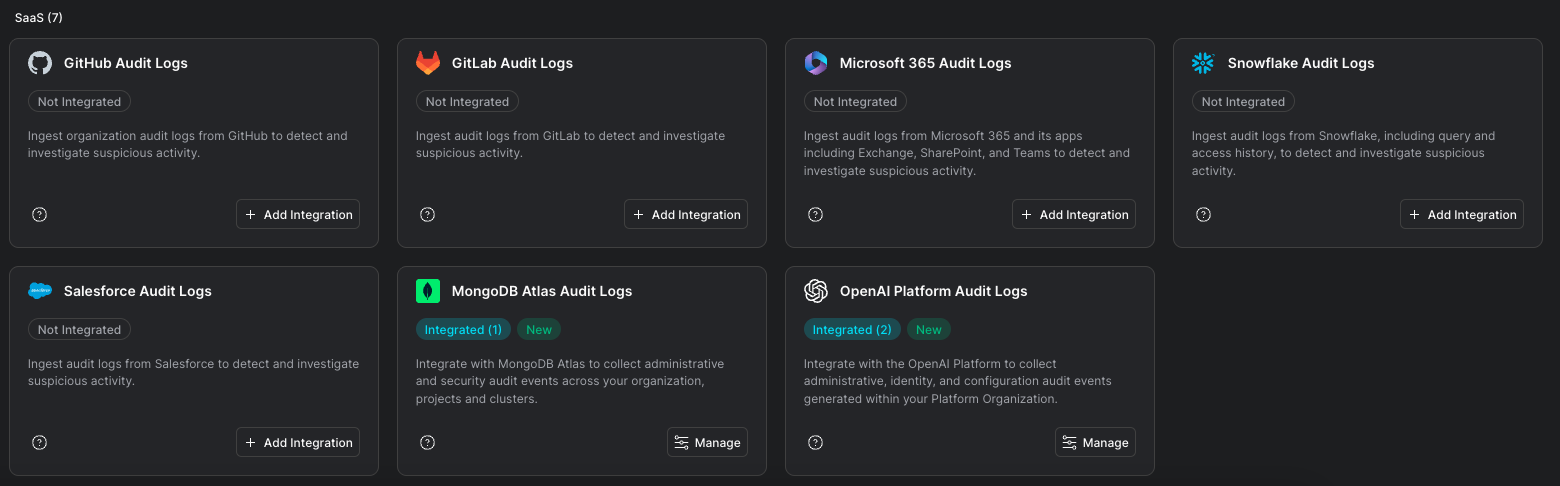
Stream Security now supports native ingestion of OpenAI Platform audit logs, extending real-time threat detection and response to your AI control plane. Security teams gain immediate visibility into sensitive administrative activity across OpenAI Platform Organizations including API key lifecycle events, service account creation, identity and role changes, project configuration updates, and security control modifications like IP allowlists and SCIM.
The integration is agentless, easy to enable, and provides out-of-the-box detections so teams can investigate and respond faster from a unified cloud security platform.
We’re excited to announce that Stream Security now supports native log ingestion from OpenAI Platform Audit Logs, bringing continuous visibility and security detections to one of the most critical layers in modern AI adoption: the AI platform control plane.
As organizations operationalize GenAI, security teams need the same rigor and monitoring they apply to cloud IAM and infrastructure - now extended to AI identities, administrative actions, and platform configuration.
The OpenAI Platform has become a foundational layer for building AI-powered products. It enables teams to move faster, scale usage seamlessly, and centralize governance across projects, users, and API access.
But that velocity introduces a new and highly sensitive control plane, one that is often under-monitored.
With that acceleration comes a new attack surface:
Without continuous monitoring of these control-plane actions, organizations risk missing early indicators of compromise. Unauthorized access, misconfigurations, and privilege abuse can persist undetected, especially during rapid experimentation, onboarding of new teams, and frequent configuration changes common in AI development.
With Stream Security’s OpenAI integration, security teams can:
The OpenAI Platform Audit Logs integration enables detection of high-risk activity, including:
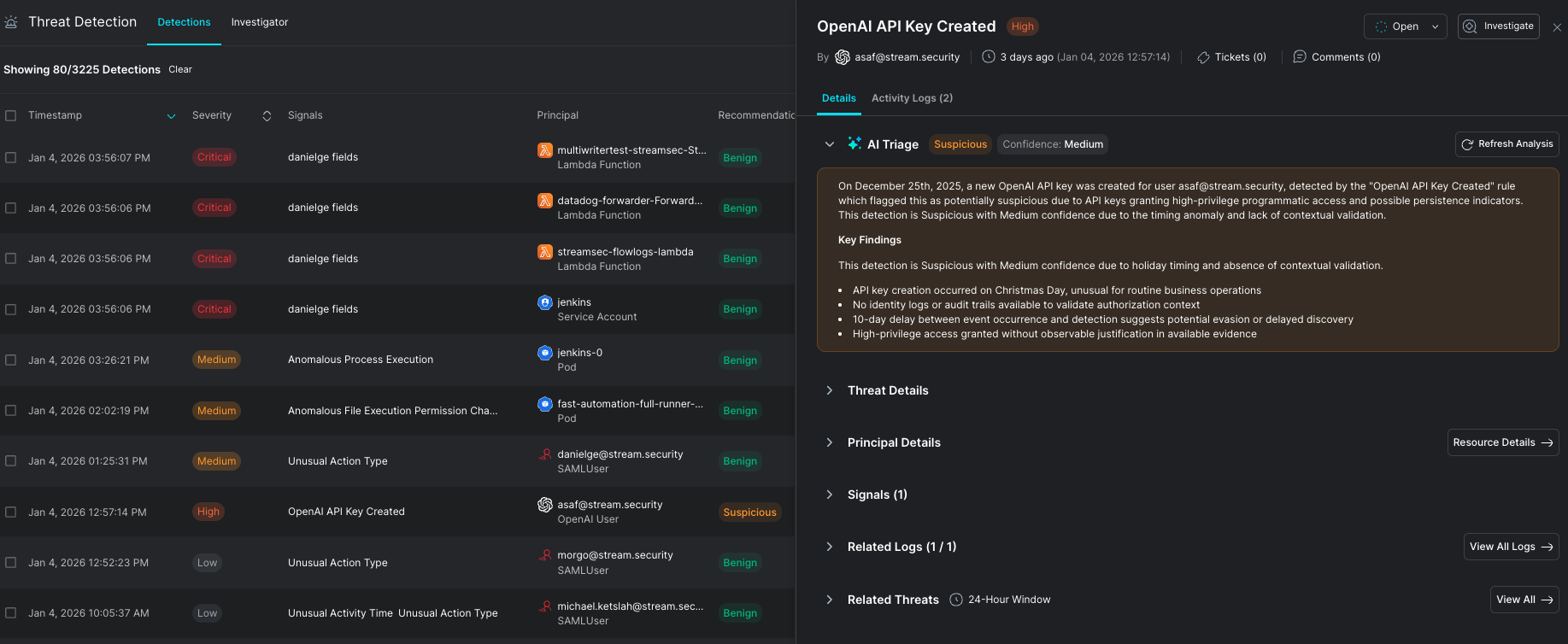
Getting started is straightforward. Stream Security ingests OpenAI Platform audit logs through a native integration, requiring no agents or infrastructure changes. Once connected, security teams gain immediate visibility into administrative, identity, and configuration activity across their OpenAI Platform organization, with out-of-the-box detections tuned for AI platform–specific threats.
The integration works alongside your existing Stream Security deployment, enriching your cloud security posture with AI control-plane visibility and enabling unified investigation across your entire cloud environment.
This release reflects Stream Security’s commitment to protecting the full cloud stack, including the platforms where AI access, identities, and permissions are managed.
AI applications don’t exist in isolation, and neither should your security monitoring. With OpenAI Platform audit visibility inside Stream Security, teams can extend detection and response to the control plane where some of the highest-impact changes occur.
If you’re using the OpenAI Platform and want continuous visibility into administrative activity, identity changes, and configuration risk, we’d love to show you how the integration works.
Book a demo to learn more about enabling OpenAI Platform audit log ingestion for your organization.
Stream Security is an AI Detection & Response (AI DR) company built for the era of AI-driven environments across cloud, on-prem, and SaaS. As AI agents operate with real permissions and attackers move at machine speed, Stream enables security teams to keep pace by continuously computing a real-time, deterministic model of their entire environment. Powered by its CloudTwin® technology, Stream instantly understands the full impact of every action across identities, permissions, networks, and resources, allowing organizations to detect, prioritize, and safely respond to threats before they propagate. This transforms security from reactive detection into a true control plane for modern infrastructure.
