Enriching Real-Time Cloud Detection & Response with Workload Observability: A Vendor Agnostic Approach


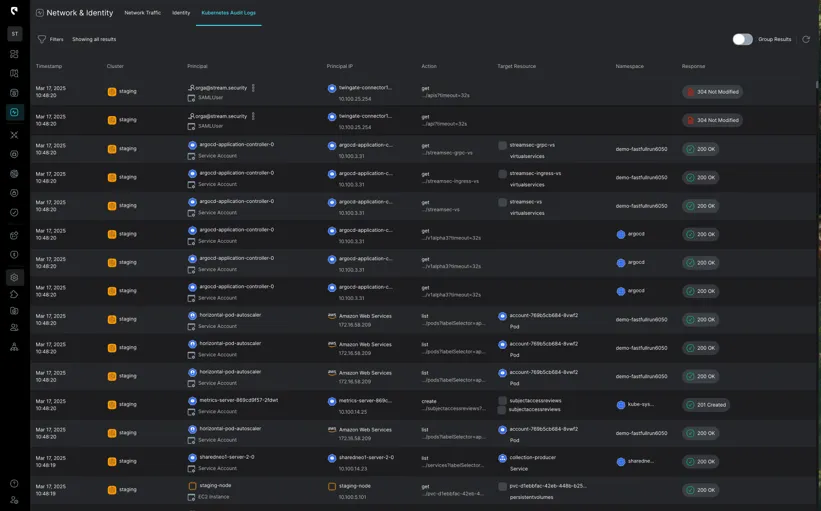
At Stream.Security, we believe the foundation of robust Cloud Detection and Response (CDR) lies in real-time visibility across your entire multi-cloud environment. That’s why our unique approach starts with an agentless methodology, creating a real-time model of your cloud infrastructure to provide immediate insights into attacks at the network, identity, and application log layers.
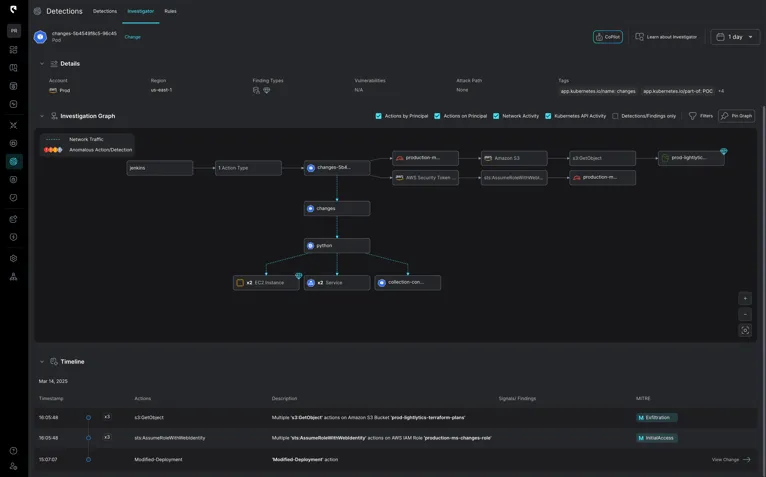
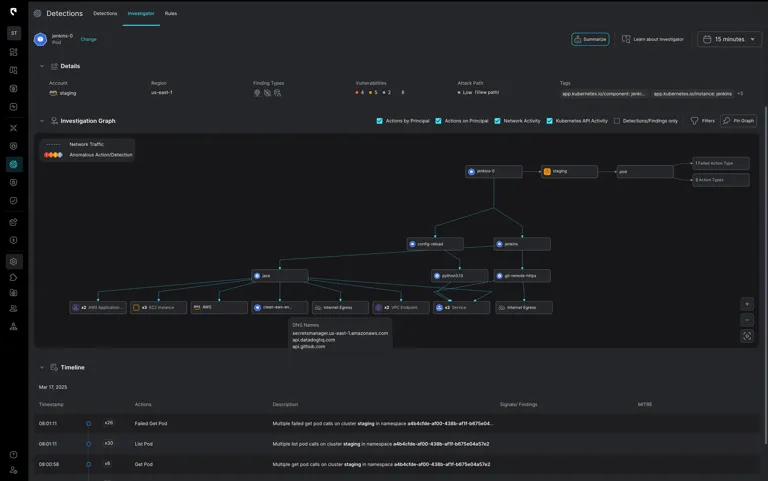
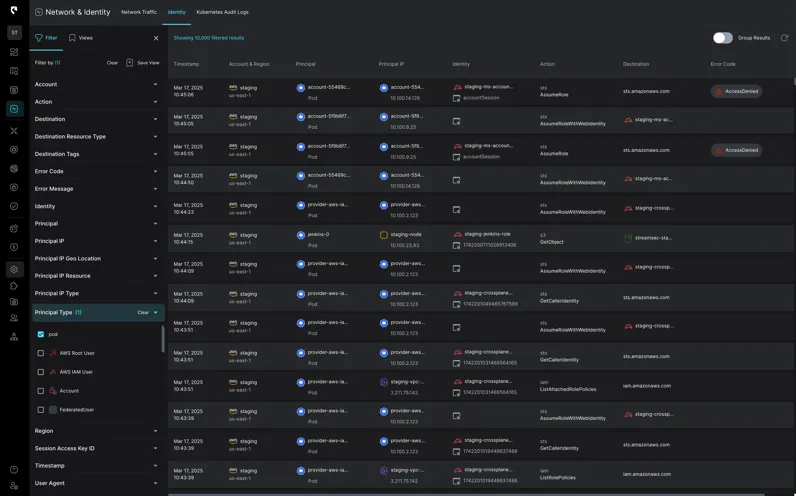
At Stream.Security, we believe the foundation of robust Cloud Detection and Response (CDR) lies in real-time visibility across your entire multi-cloud environment. That’s why our unique approach starts with an agentless methodology, creating a real-time model of your cloud infrastructure to provide immediate insights into attacks at the network, identity, and application log layers. This foundational layer which is enabled by Stream’s CloudTwin is critical because it gives SecOps teams a comprehensive understanding of an attack as it unfolds, spanning network traffic, user and machine behavior, infrastructure changes, and application activity.
This contrasts sharply with building CDR on top of traditional posture management tools that rely on periodic scans or snapshots. These approaches inherently create blind spots, leaving you vulnerable to threats that evolve between scans. Our agentless, real-time approach eliminates these gaps, providing continuous visibility into the attacks.
However, even with this broad visibility, there are scenarios where deeper, workload-level insights are beneficial. One of the major benefits of marrying cloud workload posture with real time detection and response is eliminating the silos that often exist between SecOps, Cloud Security, and DevOps. These gaps are increasingly prompting CISOs to seek platforms that foster collaboration and efficiency to limit blind spots and accelerate MTTR.
That's why we offer two powerful ways to extend our real-time CDR platform with workload observability:
Stream allows enterprises to reduce total cost of ownership while preventing vendor lock-in when an organization's security ecosystem dictates a best of breed approach versus the platformatization that many organizations are becoming increasingly wary of.
While our agentless approach provides a holistic view, integrating with agents at the workload level offers granular insights into what's happening within your Kubernetes pods and containers. For customers who don’t have an existing agent solution for workload management, Stream is pleased to introduce integration with Tetragon’s eBPF agent. This is where the power of eBPF (extended Berkeley Packet Filter) comes into play. eBPF allows for safe and efficient monitoring of kernel-level events, providing a rich stream of data about process executions, network connections, file access, and system calls.
This additional layer of observability is invaluable for:
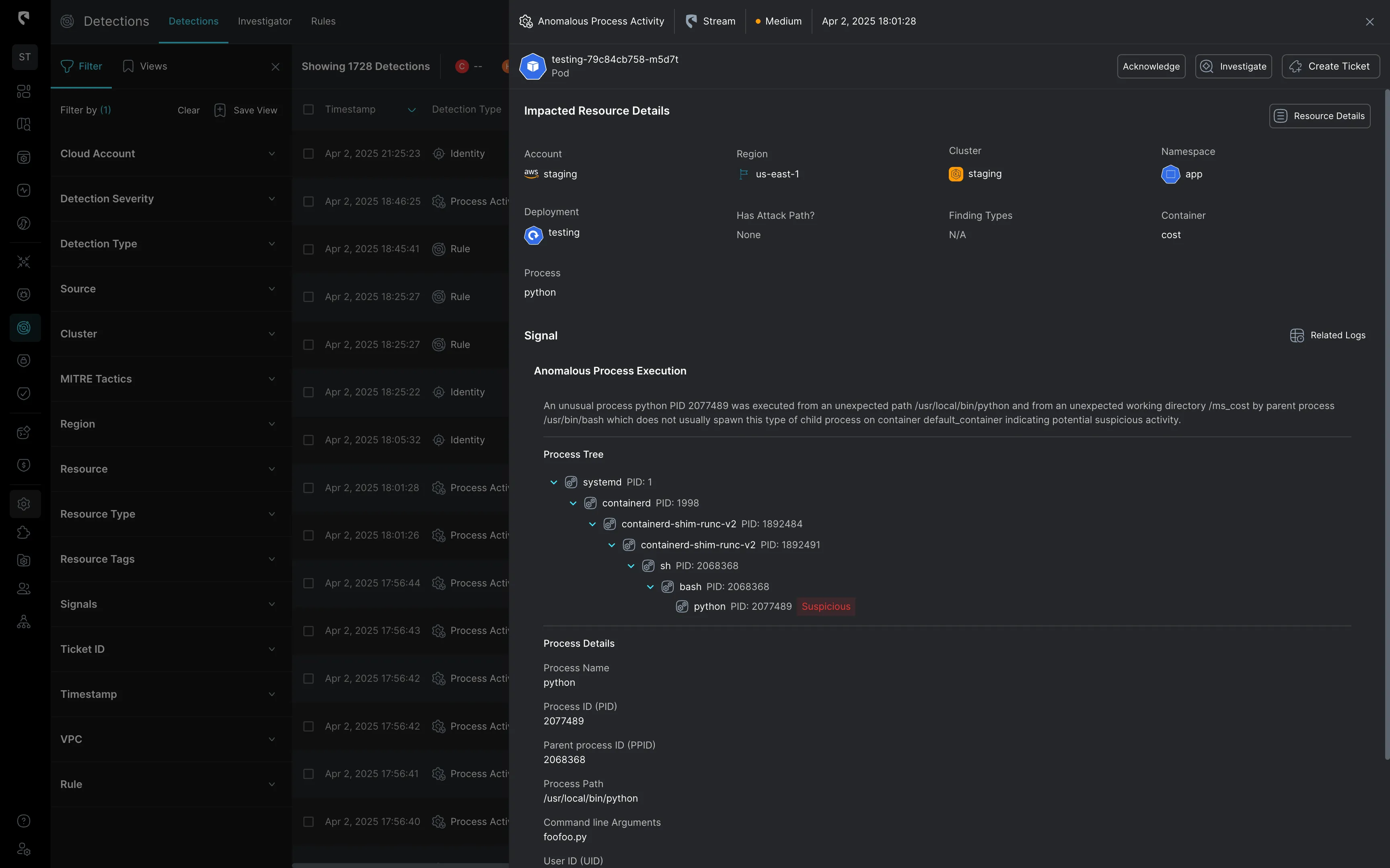
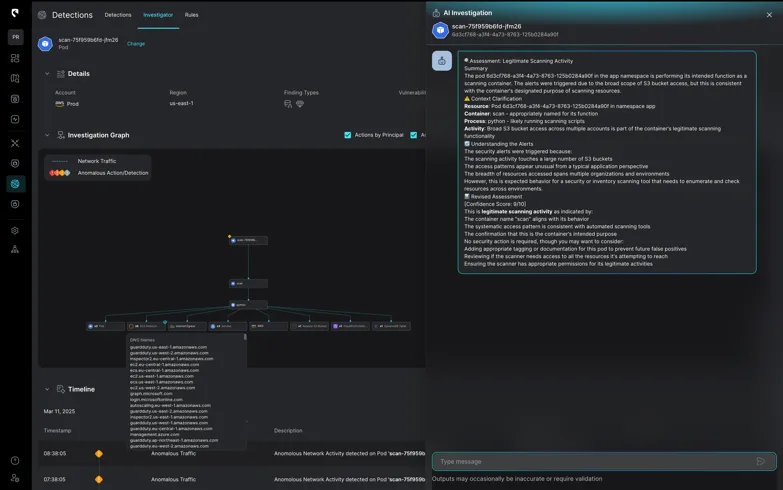
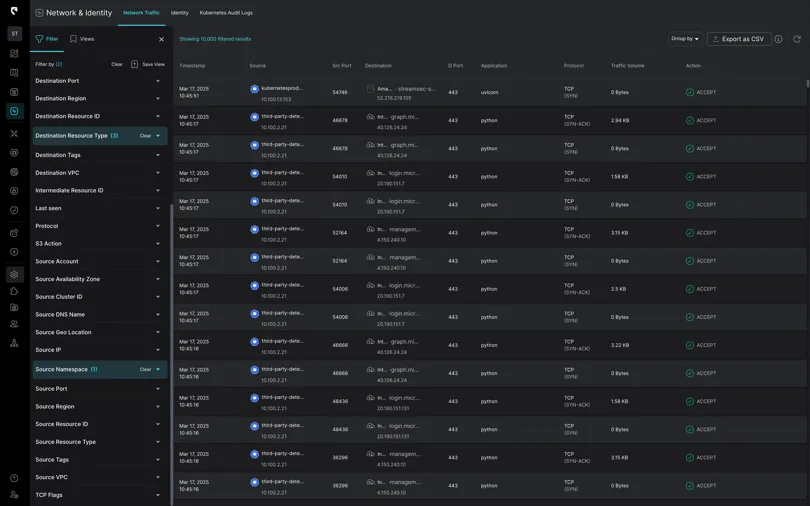
By combining our unique real-time, agentless approach with the power of workload observability, Stream Security provides the most comprehensive CDR solution on the market today. Here’s why our “Bring your own agent” approach is a game-changer:
Stream is committed to providing cutting-edge solutions that empower organizations to secure their cloud environments effectively. By extending our real-time, agentless platform with flexible workload observability options, we are equipping SecOps teams with the most comprehensive and adaptable CDR solution available. Embrace the future of cloud security with Stream.Security.
Learn more about Stream’s agent integration here.
Interesting in learning more about how Stream brings workload visibility together with complete cloud context? Book a demo with our team today.
Stream Security is an AI Detection & Response (AI DR) company built for the era of AI-driven environments across cloud, on-prem, and SaaS. As AI agents operate with real permissions and attackers move at machine speed, Stream enables security teams to keep pace by continuously computing a real-time, deterministic model of their entire environment. Powered by its CloudTwin® technology, Stream instantly understands the full impact of every action across identities, permissions, networks, and resources, allowing organizations to detect, prioritize, and safely respond to threats before they propagate. This transforms security from reactive detection into a true control plane for modern infrastructure.
