.png)
Is Your SOC Team Ready to Pass Cloud KYC?


If you don’t know your cloud, you can’t secure it. Alerts and AI don’t help much without real context. “Know Your Cloud” (KYC) is about understanding what you actually have, who and what can access it, and what could go wrong. Get that right, and detection makes sense, AI gets smarter, and response gets better.
In fintech, KYC (Know Your Customer) is how organizations verify identity, establish trust, and manage risk. It’s the foundation of every secure transaction. Without KYC, banks and payment providers are flying blind, exposed to money laundering, fraud, and regulatory risk.
The same principle applies to cloud security operations. Most SOCs only “see” when alerts trigger. But in the cloud, the baseline itself, which includes ephemeral resources, role chaining, serverless functions, and SaaS APIs, is a moving target. If you don’t know your cloud, every detection or AI triage is just guesswork.
“Know Your Cloud” is the process of establishing identity, context, and trust in your cloud footprint as the prerequisite for security operations.
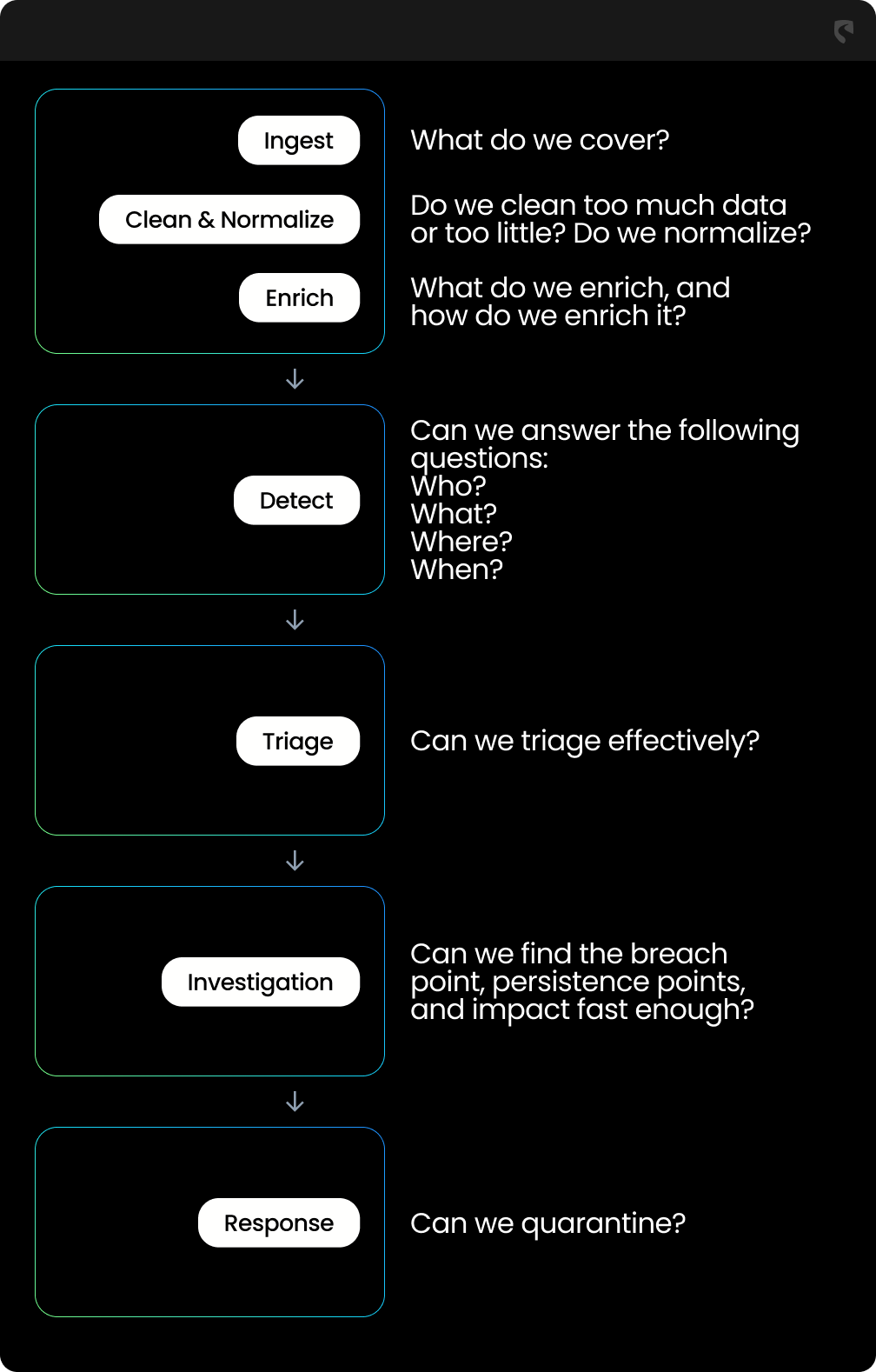
Pass/Fail Mindset:
.png)
Know Your Assets
Know Your Identities
Know Your Configurations
Know Your Risks
Know Your Telemetry
Know Your Detections
Know Your Responses
Without KYC for cloud SecOps:
Once you Know Your Cloud, you get:
Take the quiz to your team and see where you stand.
Stream Security is an AI Detection & Response (AI DR) company built for the era of AI-driven environments across cloud, on-prem, and SaaS. As AI agents operate with real permissions and attackers move at machine speed, Stream enables security teams to keep pace by continuously computing a real-time, deterministic model of their entire environment. Powered by its CloudTwin® technology, Stream instantly understands the full impact of every action across identities, permissions, networks, and resources, allowing organizations to detect, prioritize, and safely respond to threats before they propagate. This transforms security from reactive detection into a true control plane for modern infrastructure.
