The Problem
Layering AI on legacy tools doesn't fix the underlying data problem, it inherits it.

Patent Pending
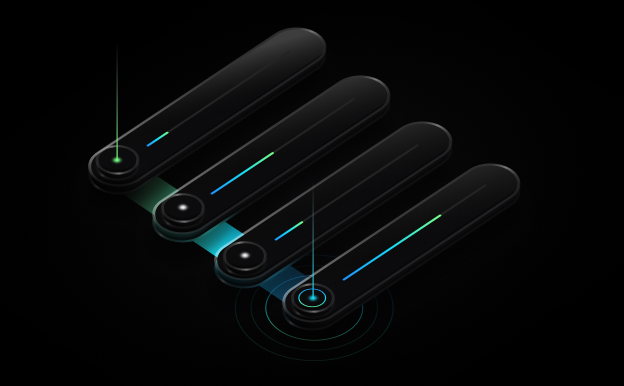
CloudTwin continuously computes the real-time state of your entire environment, cloud and data center.
Workloads, applications, agents, data stores, identities, and network paths are all modeled live.
Context and risk are correlated to behavior at ingest speed, so every human and agent-driven decision is context-complete.
CloudTwin doesn't analyze signals. It computes the system itself. When something happens, the consequence is already known. No blind spots. No waiting for context that should have been there from the start.
Context. Tools. Harness.
Everything your team and AI needs to move faster than modern threats
Protect Cloud, Kubernetes, VMware, IdP, and SaaS environments with comprehensive MITRE ATT&CK coverage. AI continuously expands detection coverage while automatically tuning and triaging alerts to reduce noise and accelerate response.
See every agentic workload in real time, its behavior, prompts, tools and full blast radius. Detect threats as they happen, powered by native AI audit logs and deep runtime telemetry.

AI uses real-time CloudTwin context to triage every finding automatically, taking you from 35% to 95% coverage without adding headcount.

StreamForce enables organizations to build, run, and scale agentic workflows on top of the CloudTwin system model, delivering precise, machine-speed responses governed by your business logic.
A live model of every workload, agent, identity, permission, and network path, so you and your AI see your exact exposure and every lateral movement path before an attacker does.
No queries. No manual correlation. Just instant, full-context attack storylines, from entry point to blast radius, so humans can validate agentic decisions in real-time.
Stream maintains a complete, real-time representation of every workload, AI agent, datastrore, network, and identity, along with their configuration, posture, risk and activity.
All logs are normalized accross your entire footprint to a common index format.
Every log is enriched with real-time asset context, risk, IP intelligence, IOC correlation and MITRE.
Every log is automatically mapped to its originating actor.
The impact of every configuration change is calculated in real time, providing immediate insight.
Uncover correlations between configuration changes, their impact, and active threats.
Detect threats early, bring your existing EDR/CWP detections into one unified, context-aware platform.
AI uses real-time context to eliminate noise, ensure full coverage, and surface attacks early.
eBPF sensors capture network, API, process, and file activity to detect AI and application threats.
Detections fire at the speed of log ingestion, reducing MTTD by 60% compared to traditional solutions.
Trace back to the exact moment and method of compromise.
Detect everything while eliminating false positives with your cloud’s live state.
Every asset comes with complete environmental context and relationships.
AI-powered insights with human oversight and decision-making authority.
Response procedures tailored to resource specific state.
Minimize downtime with AI analysis that understands business impact.
Intelligent recommendations with human verification.
Instantly rollback malicious configuration changes that are out of allowed posture.
Integrations