When most organizations think about efficient cloud environment, they are often thinking about cost efficiency, security and Infrastructure as code maintenance – the lower the cost for a functioning, secured, IaC managed cloud setup, the better.
However, there is one thing that’s often overlooked by many, particularly by those outside of the DevOps team that maintains the cloud environment: networking.
The complexity of cloud networking has increased in the past few years, and it seems like it is going to provide challenges in the years to come.
All cloud operations run on an underlying networking setup, which makes networking a very crucial component in every cloud environment.
During re:Invent 2021, AWS announced the VPC Network Access Analyzer. A new tool that uses Network Access Scopes to specify the desired connectivity between your AWS resources.
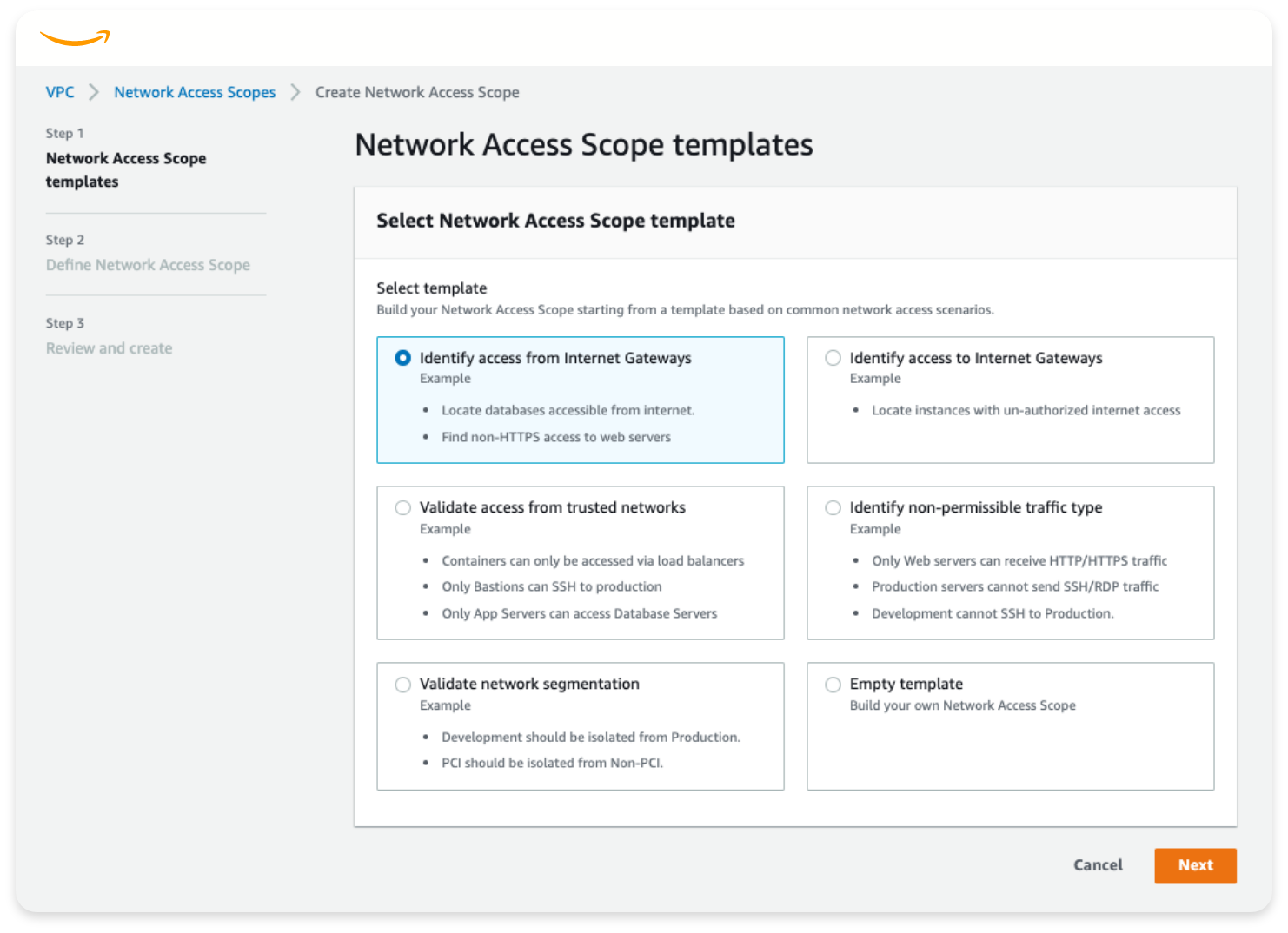
The Network Access Analyzer is a feature that identifies unintended network access to your resources on AWS. You can use Network Access Analyzer to specify your network access requirements and to identify potential network paths that do not meet your specified requirements. You can use Network Access Analyzer to:
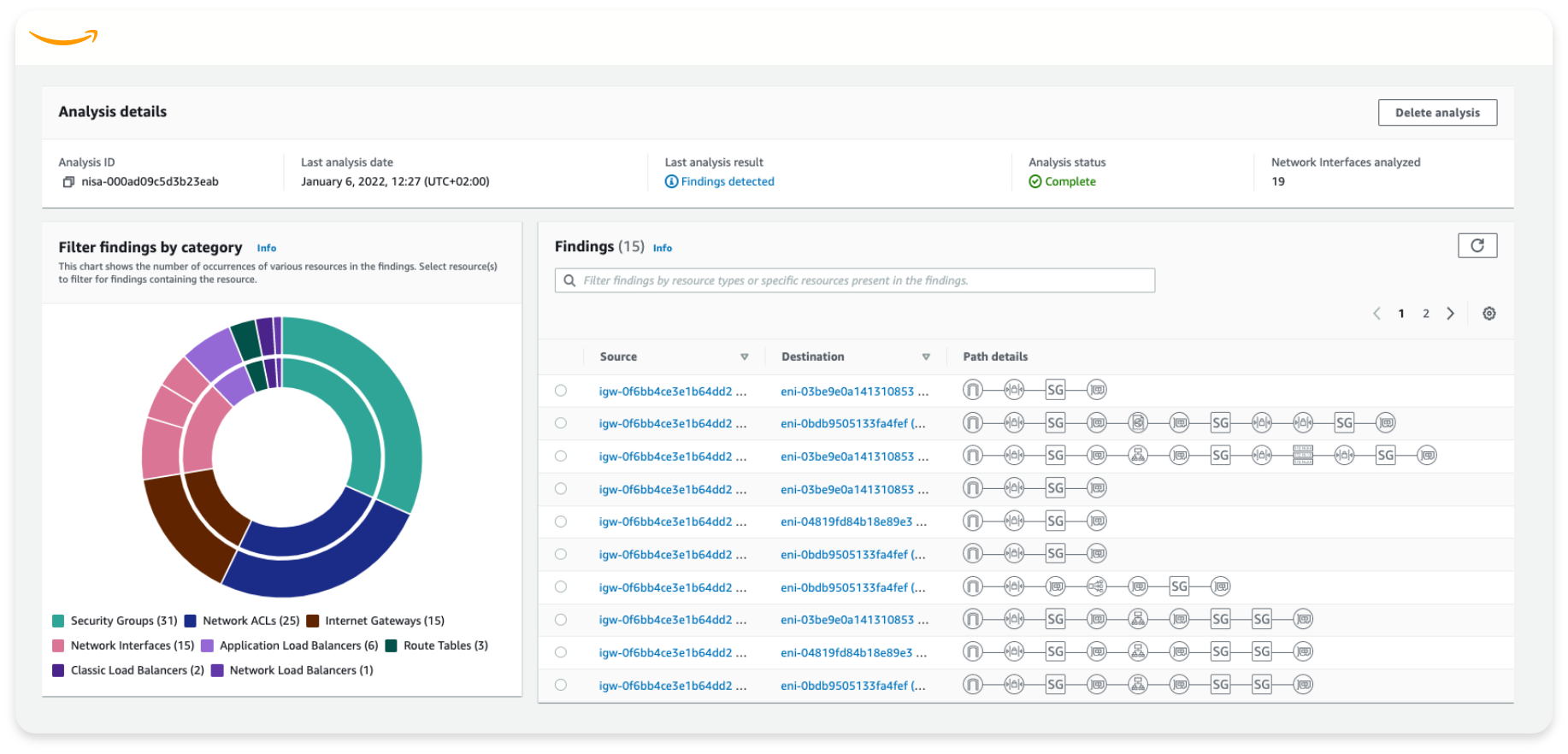
The release of the network access analyzer proves that creating and maintaining an efficient and secured network is one of the major pain points for most organizations these days. This feature is a descent way to understand the vulnerabilities in your network topology, however, it has several limitations and it is unable to provide organizations the most informative answers to their queries and needs.
This is where Stream.Security jumps in.
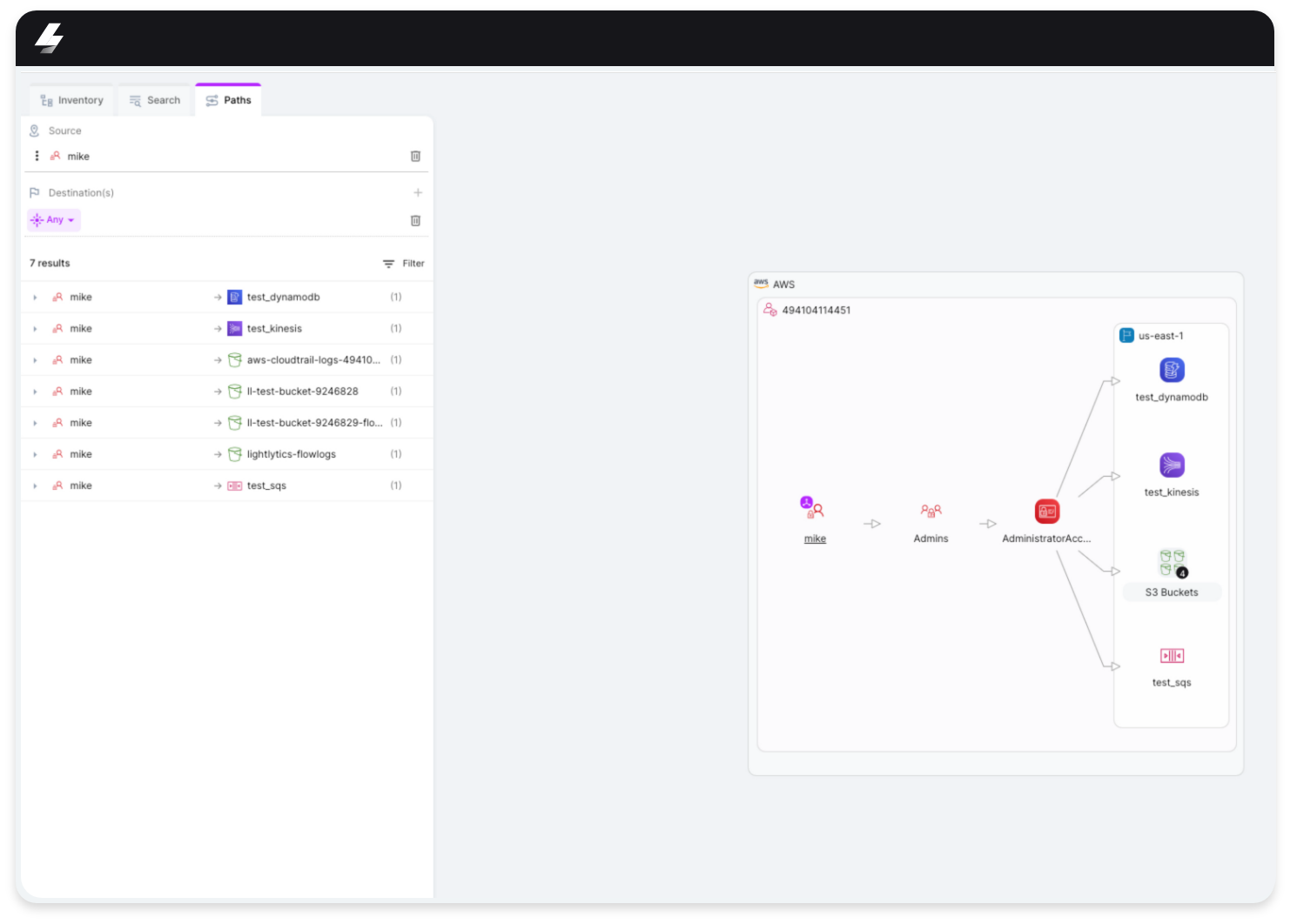
Stream.Security is using the most sophisticated methods and technologies to provide a full picture regarding your cloud posture, as well as the ability to get the most out of your actions in the platform.
When integrating a new AWS account, Stream.Security is scanning the desired regions for resources’ configurations and inserts them into our highly complex mathematical model.
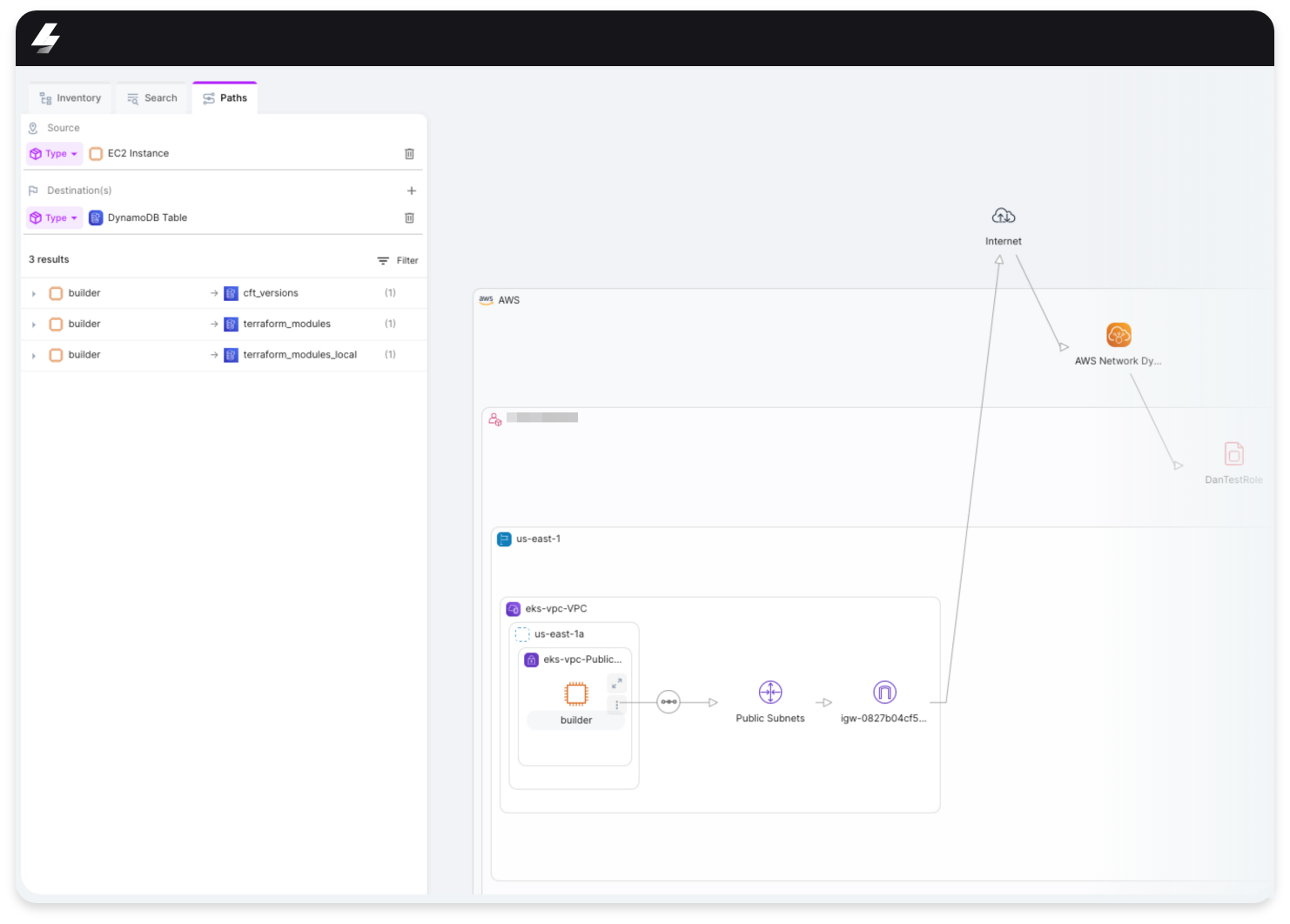
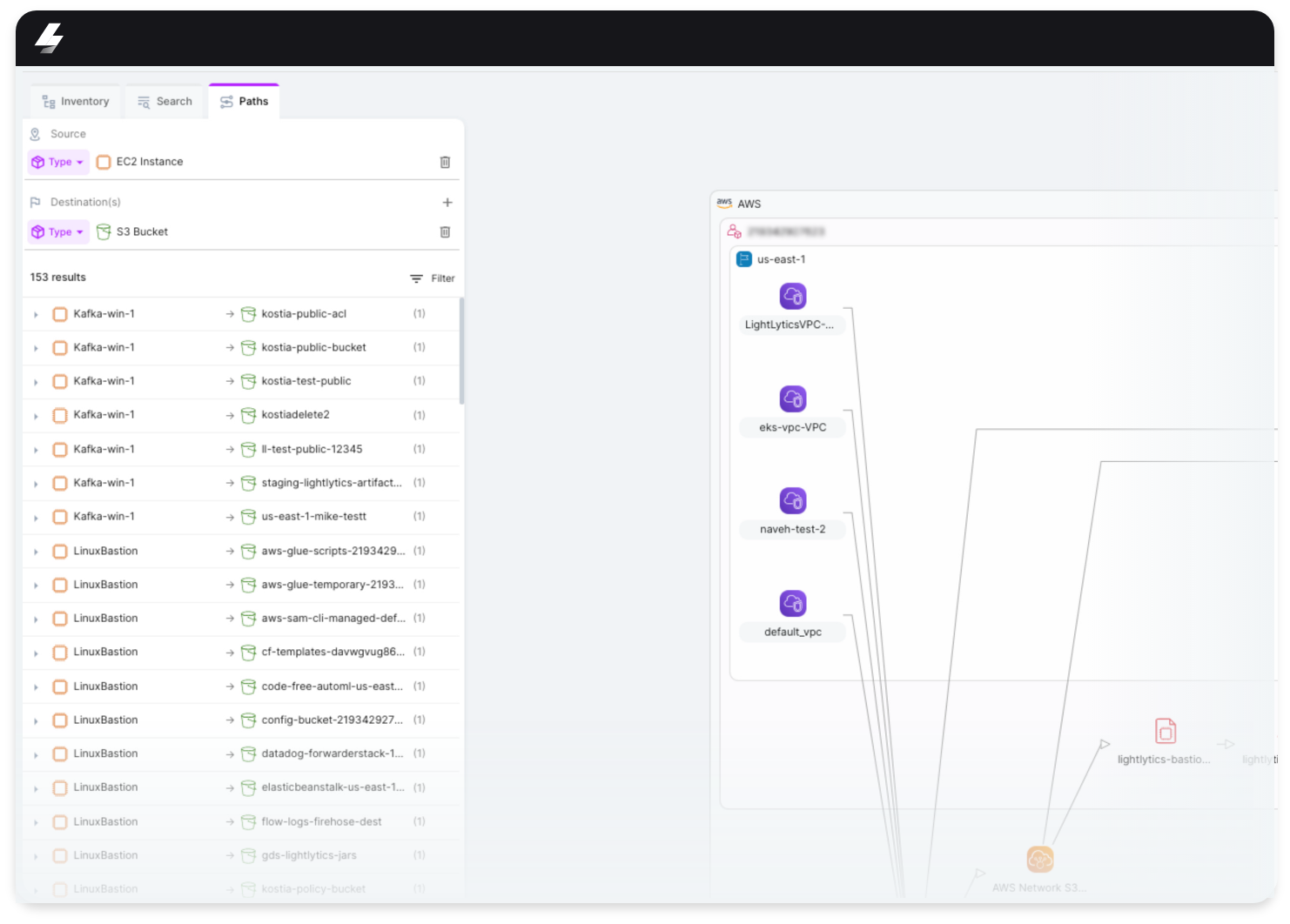
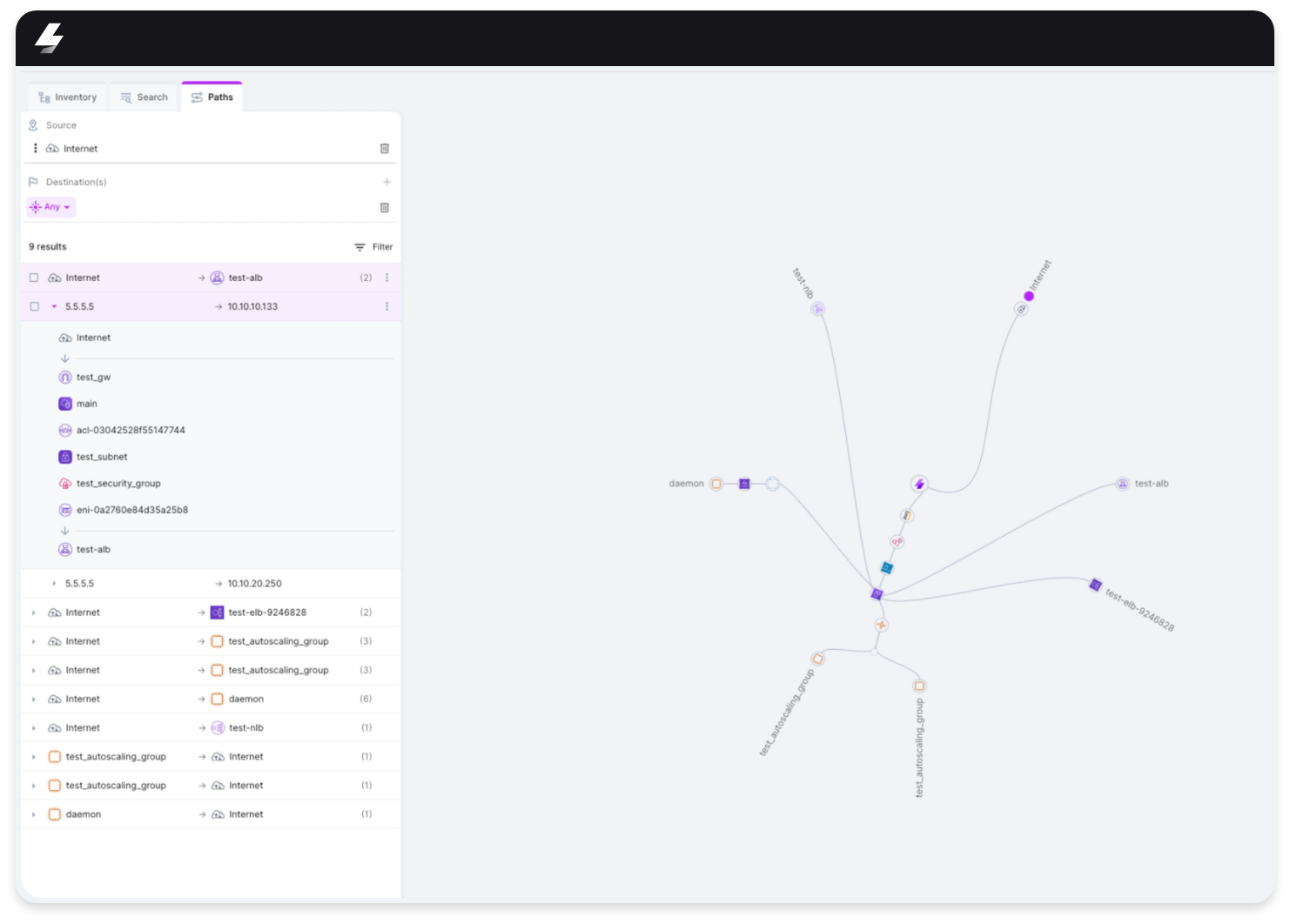
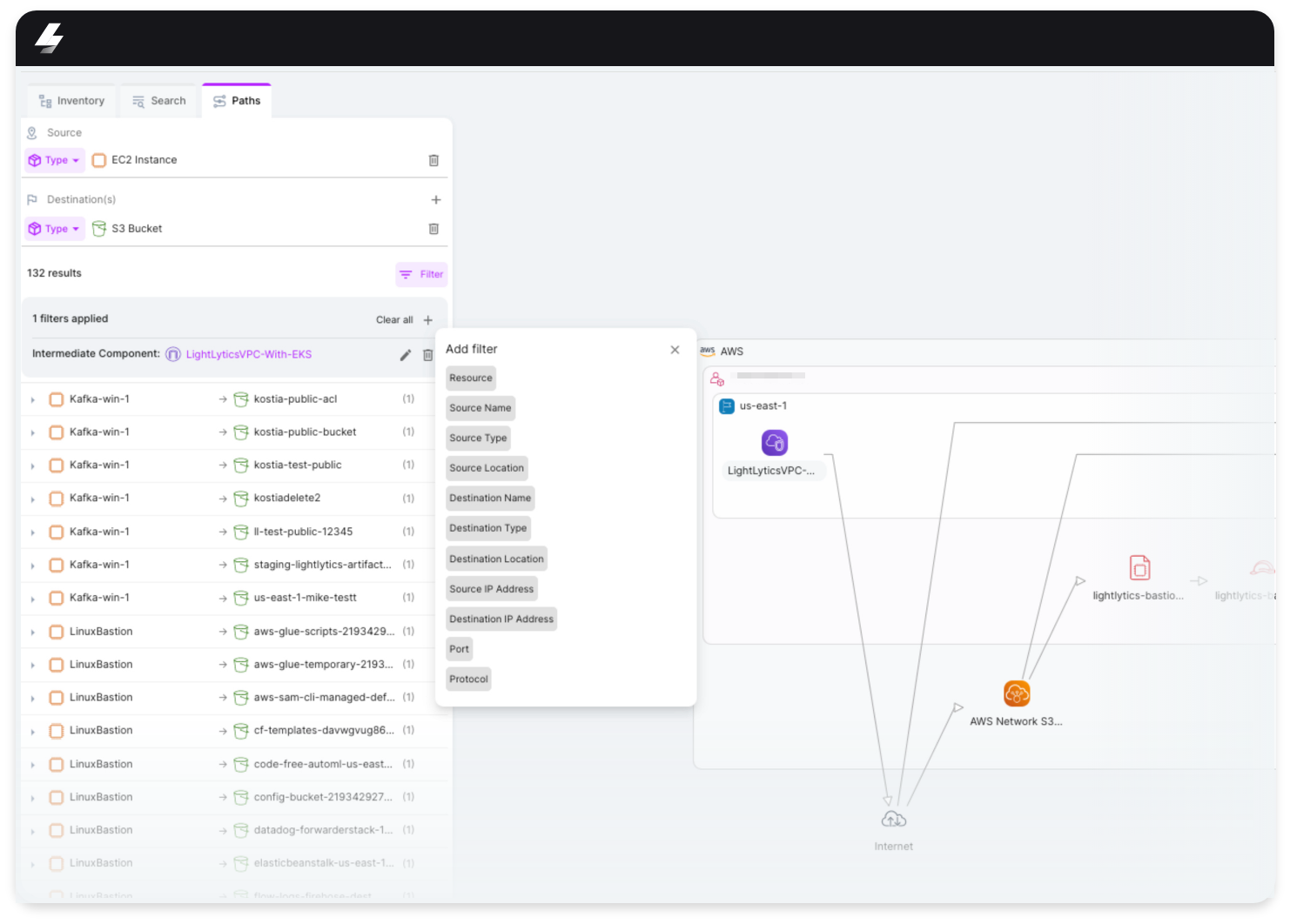
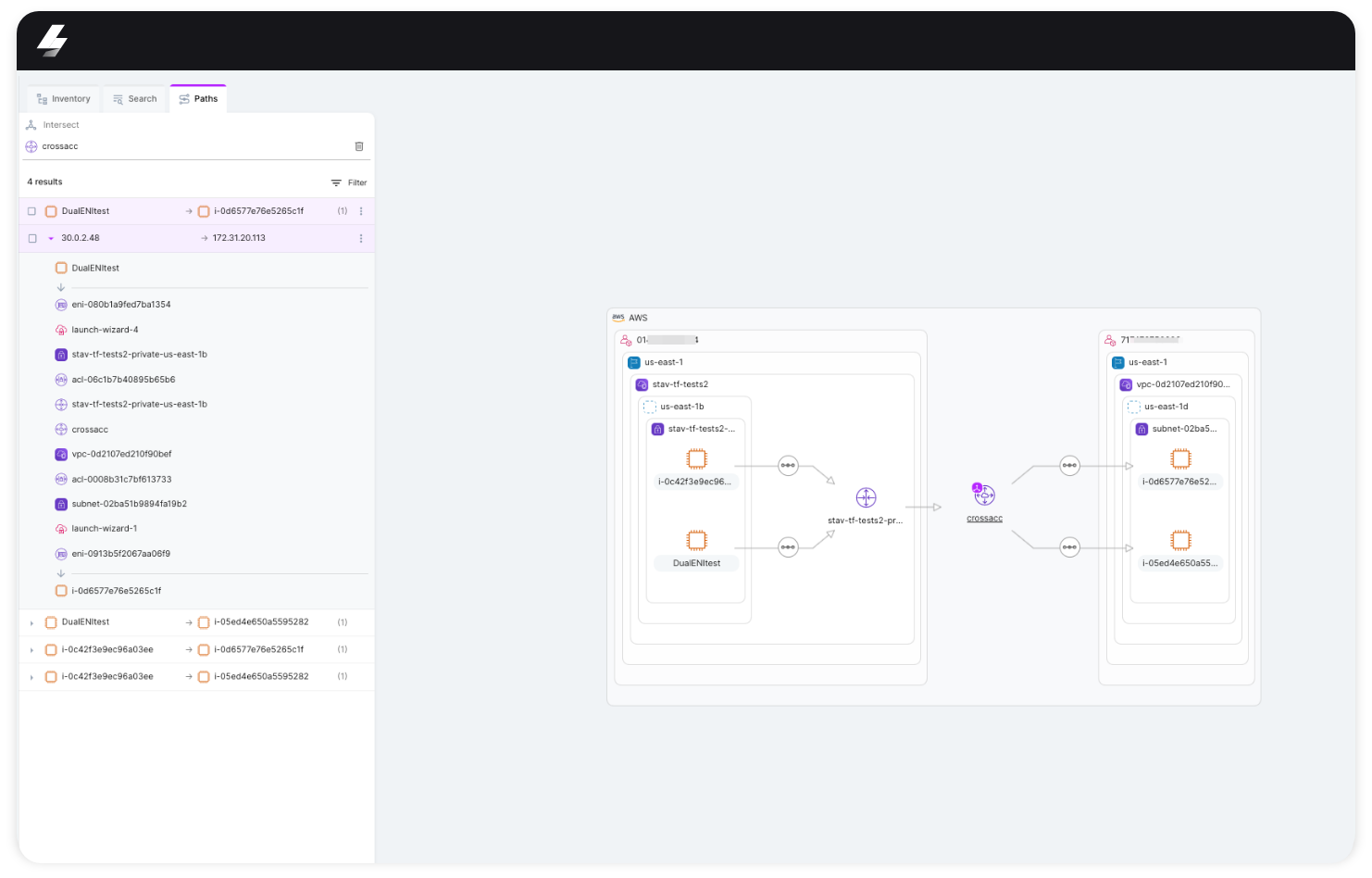
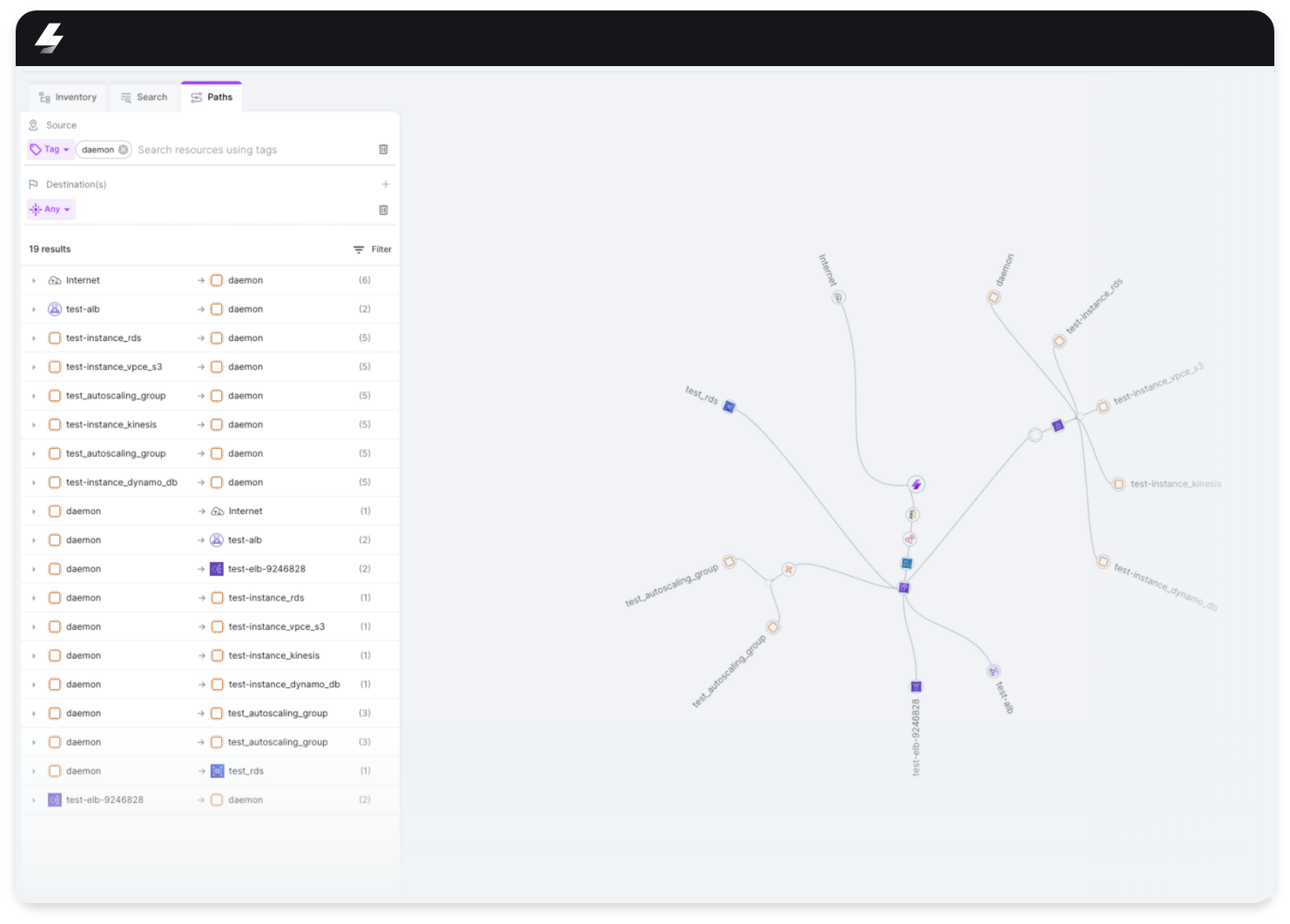
Immediately Stream.Security understands the different relationships and dependencies between all your cloud resources. In addition, Stream.Security is making sure that the cloud posture in our platform is always updated in real time. We display an actual representation of your cloud posture in real time, with the ability to query the system for source and destination reachable connections, according to your business logic.
There are more than a few unique and important capabilities that can only be provided by Stream.Security Discovery:

And the best for last: Application Behavior!
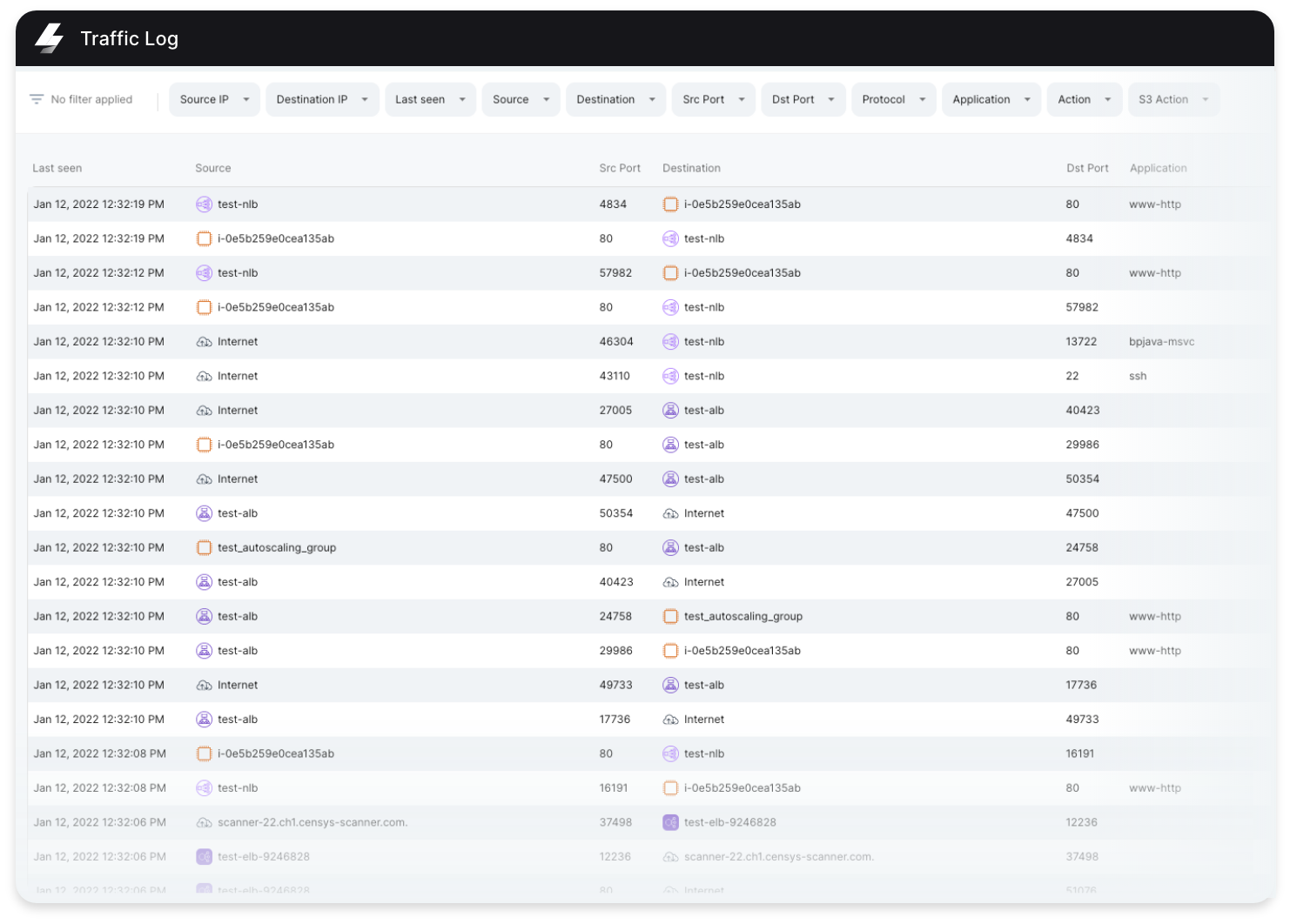
On top of all the above, Stream.Security has the ability to collect VPC Flowlogs and S3 Access logs and utilize them into our Discovery and impact analysis.
Stream.Security enrich the IP traffic in your cloud environment and allow our users to statically examine them in real time across VPCs, Buckets and even specific connections
By using Stream.Security Discovery, you can easily gain control over existing infrastructure, design changes in AWS in an efficient manner and embrace the shift left approach by allowing non-infrastructure engineers to better understand the organization’s cloud environment.
We have a lot more existing capabilities and great things to come!
Sign up now and get your 14 days free trial
Stream Security is an AI Detection & Response (AI DR) company built for the era of AI-driven environments across cloud, on-prem, and SaaS. As AI agents operate with real permissions and attackers move at machine speed, Stream enables security teams to keep pace by continuously computing a real-time, deterministic model of their entire environment. Powered by its CloudTwin® technology, Stream instantly understands the full impact of every action across identities, permissions, networks, and resources, allowing organizations to detect, prioritize, and safely respond to threats before they propagate. This transforms security from reactive detection into a true control plane for modern infrastructure.
